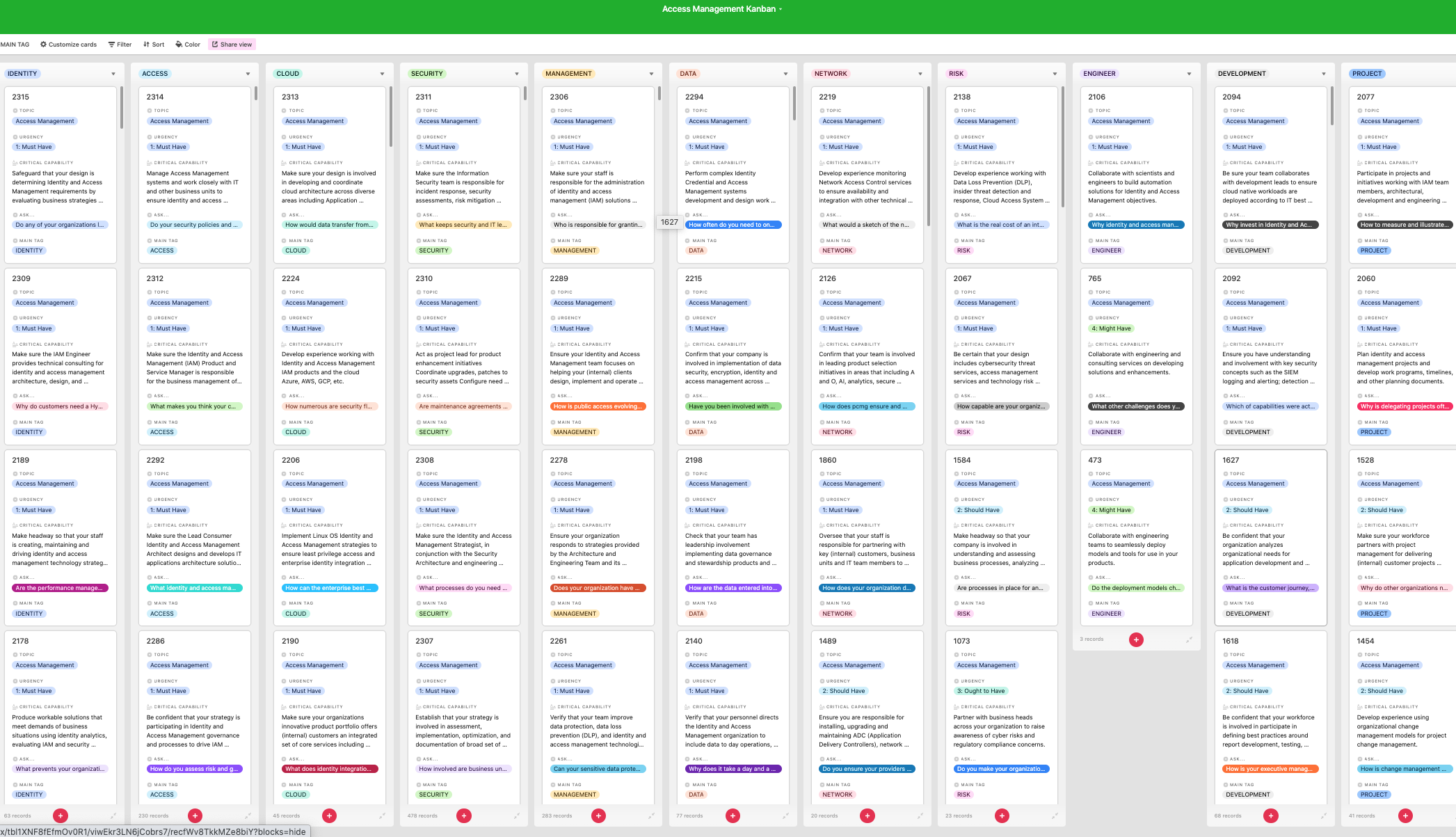
Look inside the Kanban:
https://theartofservice.com/Access-Management-kanban
 Safeguard that your design is determining Identity and
Safeguard that your design is determining Identity and
Access Management requirements by evaluating business strategies and requirements, implementing IAM and information security standards, conducting system and vulnerability analyses and risk assessments, recommending secure architecture aligned to business architecture, and identifying/driving remediation of integration issues in IAM.
Benefits of the Access Management Kanban
- Does your organization have a user access management system as a single sign on system that solutions can be integrated with?
- Do you have Identity and Access Management methods in place to ensure appropriate access to organization applications and services when working remotely?
- As more organizations move to a hybrid cloud model, how does the Zero Trust model and Identity and Access Management technologies ensure that data is protected?
- Does your organization have an Identity Access Management platform for cloud tools, data, and service interfaces?
- Are there any other identity repositories other than AD that the Identity Access Management solution will have to integrate with?
- At what point in a project lifecycle does the business engage your IT Security or Identity & Access Management teams?
- Does your organization have Identity and Access Management solution and configurations centralized in a single place?
- In the next year, how do you anticipate that the focus on workforce Identity and Access Management will change within your organizations security team?
- Does your organization have Identity and Access Management policies and procedures documented?
- Does your organization have identity and automated access management in place to initiate and deactivate access as people move into and out of your organization?
Summary
The Art of Service has identified and prioritized 2315 Access Management critical capabilities and use cases to assess and use. Leaders can select those results that best align with their business needs before implementing a solution.
The Art of Service's Critical Capabilities evaluates and prioritizes hundreds of results to help with the outcome selection process.
This Critical Capabilities Kanban will enable leaders to shortlist hundreds of appropriate results fast, because they are uniquely ready-to-use prioritized, starting with the 'Must Have' category; the most urgent and critical priorities.
This Kanban will help you plan and manage your Access Management roadmap.
- Transform the data into actionable views for your organization: business data changes, so how you view it should be flexible. Create the perfect view that's right for you.
- Put your workflows on autopilot: Help your team go faster and focus on what matters by automating your processes. Upload and use the Kanban with your favorite apps and services like Asana, Airtable, Basecamp, Monday.com, Atlassian, Trello etc.
- Knock down data silos: Align your teams around a single source of truth with real-time data from different sources. Point. Click. Stay in Sync.
- Use it's flexible reporting for your unique use case: Whether you're "no-code" or you "know-code", the Kanban is the foundational tool to show what you want to who needs to see it.
Included in your instant download purchase are the following digital products:
As seen in the Kanban above, the complete 2315 Access Management critical capabilities and use cases, their prioritization, workflows, tagging and questions.
The download is available as an easy to re-use Excel format, which you can use as is, or import in any management tool of your choice, like Monday.com, Atlassian, Smartsheet, Power BI, Asana, Airtable etc.
Also included is the Access Management critical capabilities Book in PDF format covering all the criteria including ideas for (potential) roles to assign the criteria to. Table of contents:
About The Art of Service
Access Management Critical Capabilities, Meaningful Metrics And Their Prioritization
Background
Prioritization Of Requirements
The Prioritization Categories Are:
- Must Have
- Should Have
- Ought to Have
- Might Have
- Could Have
Use In New Product/Service/Process Development
Benefits
The Critical Access Management Capabilities And Their Priorities:
- Priority - Must Have #
- Priority - Should Have #
- Priority - Ought to Have #
- Priority - Might Have #
- Priority - Could Have #
Index
You're in good company. Join:
Trusted by: GSK, Indivior, Grand Leisure, Air Products, Inter-American Development Bank, Catholic Relief Services, Liberty Mutual Insurance, AstraZeneca, Emory, NYC DEPARTMENT OF BUSINESS SERV., Curium Pharma, SAGE Black Consulting & Contracting LLC, Mobis Parts America, LLC, Plaid, U.S. Bank, Oracle, Steyer, Home Depot / THD, BAE Systems, Saviynt, SBG Technology Solutions, CPS Energy, Visa, Microsoft, Expedia, Level Access, Universal Music Group, Clinton Health Access Initiative, CSH IT Service, U.S. Army Accession Command, BD, Amazon.com Services LLC, Google, Facebook, MURAL, Accenture, Access Sciences, Varen Technologies, Guardian Life Insurance Company, CertiPay, US Army Installation Management Command, FirstBank Florida, Accesso, Red Hat Software, UnitedHealth Group, Boston Consulting Group, Compass Corporate, Digi-Key Corporation, DOXA Insurance Holdings, LLC, US Defense Technical Information Center, Virginia Community College System, Williams-Sonoma-Supply Chain, US Federal Aviation Administration, UNITED PARCEL SERVICE, Bayser, KARTHIK CONSULTING, Bayser Consulting, System High Corporation, Syncreon, Intouch Solutions, Zenetex LLC, FOX Factory, Inc., Worley, Citi, Access Pharmaceutical, Jet Access Group, AccessLex Institute, Care Access, Intel, Northwestern Mutual, American Family Insurance, Franciscan Alliance, Inc., Costco Wholesale, ASRC Federal Holding Company, Saliense Consulting LLC, Eli Lilly, TIAA, Identity Fusion, Cleveland Clinic, San Francisco State University, D'Addario & Company, Enloe Medical Center, Johnson & Johnson Family of Companies, Silicon Valley Bank, Finicity, Tiffany & Co., Horizon, Bayer