Advanced Cybersecurity Strategies for Military and Defense Professionals: Protecting Against Emerging Threats
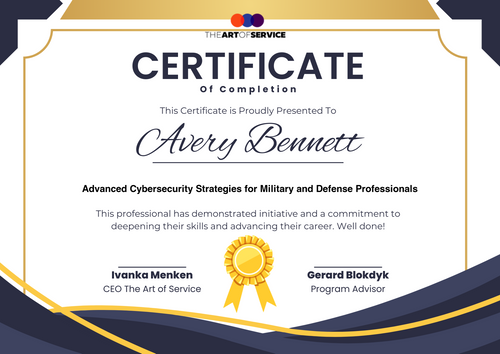
Course Overview This comprehensive course is designed to equip military and defense professionals with the knowledge and skills necessary to protect against emerging cybersecurity threats. Participants will receive a certificate upon completion, issued by The Art of Service.
Course Curriculum Module 1: Introduction to Cybersecurity
- Defining Cybersecurity: Understanding the basics of cybersecurity and its importance in the military and defense sectors
- Cybersecurity Threats: Identifying and understanding emerging threats, including malware, phishing, and ransomware
- Cybersecurity Frameworks: Overview of popular frameworks, including NIST Cybersecurity Framework and ISO 27001
Module 2: Network Security
- Network Fundamentals: Understanding network protocols, devices, and architectures
- Network Threats: Identifying and mitigating network threats, including sniffing, spoofing, and denial-of-service attacks
- Network Security Measures: Implementing firewalls, intrusion detection and prevention systems, and virtual private networks (VPNs)
Module 3: Cryptography
- Introduction to Cryptography: Understanding the basics of cryptography and its role in cybersecurity
- Types of Cryptography: Symmetric, asymmetric, and hashing algorithms
- Cryptographic Protocols: Secure Sockets Layer/Transport Layer Security (SSL/TLS) and Internet Protocol Security (IPSec)
Module 4: Incident Response
- Incident Response Planning: Developing an incident response plan and identifying incident response teams
- Incident Response Steps: Identifying, containing, eradicating, recovering, and post-incident activities
- Incident Response Tools: Using tools, such as incident response software and threat intelligence feeds
Module 5: Cloud Security
- Cloud Computing Fundamentals: Understanding cloud computing models, deployment models, and service models
- Cloud Security Risks: Identifying and mitigating cloud security risks, including data breaches and unauthorized access
- Cloud Security Measures: Implementing cloud security controls, such as encryption and access controls
Module 6: Artificial Intelligence and Machine Learning in Cybersecurity
- Introduction to AI and ML: Understanding the basics of artificial intelligence and machine learning
- AI and ML in Cybersecurity: Using AI and ML for threat detection, incident response, and predictive analytics
- AI and ML Security Risks: Identifying and mitigating AI and ML security risks, including bias and adversarial attacks
Module 7: Internet of Things (IoT) Security
- Introduction to IoT: Understanding the basics of IoT and its applications
- IoT Security Risks: Identifying and mitigating IoT security risks, including device vulnerabilities and data breaches
- IoT Security Measures: Implementing IoT security controls, such as encryption and secure communication protocols
Module 8: Cybersecurity Governance and Compliance
- Cybersecurity Governance: Understanding cybersecurity governance frameworks and best practices
- Compliance and Regulations: Understanding relevant compliance and regulatory requirements, such as GDPR and HIPAA
- Risk Management: Identifying and mitigating cybersecurity risks, including risk assessment and risk treatment
Course Features - Interactive and Engaging: Interactive lessons, quizzes, and gamification to keep participants engaged
- Comprehensive and Personalized: Comprehensive curriculum tailored to the needs of military and defense professionals
- Up-to-date and Practical: Course content is updated regularly to reflect the latest cybersecurity threats and best practices
- Real-world Applications: Real-world examples and case studies to illustrate key concepts and best practices
- High-quality Content: High-quality course content developed by expert instructors
- Expert Instructors: Experienced instructors with expertise in cybersecurity and military/defense sectors
- Certification: Participants receive a certificate upon completion, issued by The Art of Service
- Flexible Learning: Self-paced online course with flexible learning options
- User-friendly and Mobile-accessible: User-friendly and mobile-accessible course platform
- Community-driven: Private online community for discussion and networking with peers
- Actionable Insights: Actionable insights and takeaways to apply in real-world scenarios
- Hands-on Projects: Hands-on projects and exercises to reinforce learning
- Bite-sized Lessons: Bite-sized lessons for easy learning and retention
- Lifetime Access: Lifetime access to course content and updates
- Gamification and Progress Tracking: Gamification and progress tracking to monitor progress and stay motivated
Module 1: Introduction to Cybersecurity
- Defining Cybersecurity: Understanding the basics of cybersecurity and its importance in the military and defense sectors
- Cybersecurity Threats: Identifying and understanding emerging threats, including malware, phishing, and ransomware
- Cybersecurity Frameworks: Overview of popular frameworks, including NIST Cybersecurity Framework and ISO 27001
Module 2: Network Security
- Network Fundamentals: Understanding network protocols, devices, and architectures
- Network Threats: Identifying and mitigating network threats, including sniffing, spoofing, and denial-of-service attacks
- Network Security Measures: Implementing firewalls, intrusion detection and prevention systems, and virtual private networks (VPNs)
Module 3: Cryptography
- Introduction to Cryptography: Understanding the basics of cryptography and its role in cybersecurity
- Types of Cryptography: Symmetric, asymmetric, and hashing algorithms
- Cryptographic Protocols: Secure Sockets Layer/Transport Layer Security (SSL/TLS) and Internet Protocol Security (IPSec)
Module 4: Incident Response
- Incident Response Planning: Developing an incident response plan and identifying incident response teams
- Incident Response Steps: Identifying, containing, eradicating, recovering, and post-incident activities
- Incident Response Tools: Using tools, such as incident response software and threat intelligence feeds
Module 5: Cloud Security
- Cloud Computing Fundamentals: Understanding cloud computing models, deployment models, and service models
- Cloud Security Risks: Identifying and mitigating cloud security risks, including data breaches and unauthorized access
- Cloud Security Measures: Implementing cloud security controls, such as encryption and access controls
Module 6: Artificial Intelligence and Machine Learning in Cybersecurity
- Introduction to AI and ML: Understanding the basics of artificial intelligence and machine learning
- AI and ML in Cybersecurity: Using AI and ML for threat detection, incident response, and predictive analytics
- AI and ML Security Risks: Identifying and mitigating AI and ML security risks, including bias and adversarial attacks
Module 7: Internet of Things (IoT) Security
- Introduction to IoT: Understanding the basics of IoT and its applications
- IoT Security Risks: Identifying and mitigating IoT security risks, including device vulnerabilities and data breaches
- IoT Security Measures: Implementing IoT security controls, such as encryption and secure communication protocols
Module 8: Cybersecurity Governance and Compliance
- Cybersecurity Governance: Understanding cybersecurity governance frameworks and best practices
- Compliance and Regulations: Understanding relevant compliance and regulatory requirements, such as GDPR and HIPAA
- Risk Management: Identifying and mitigating cybersecurity risks, including risk assessment and risk treatment