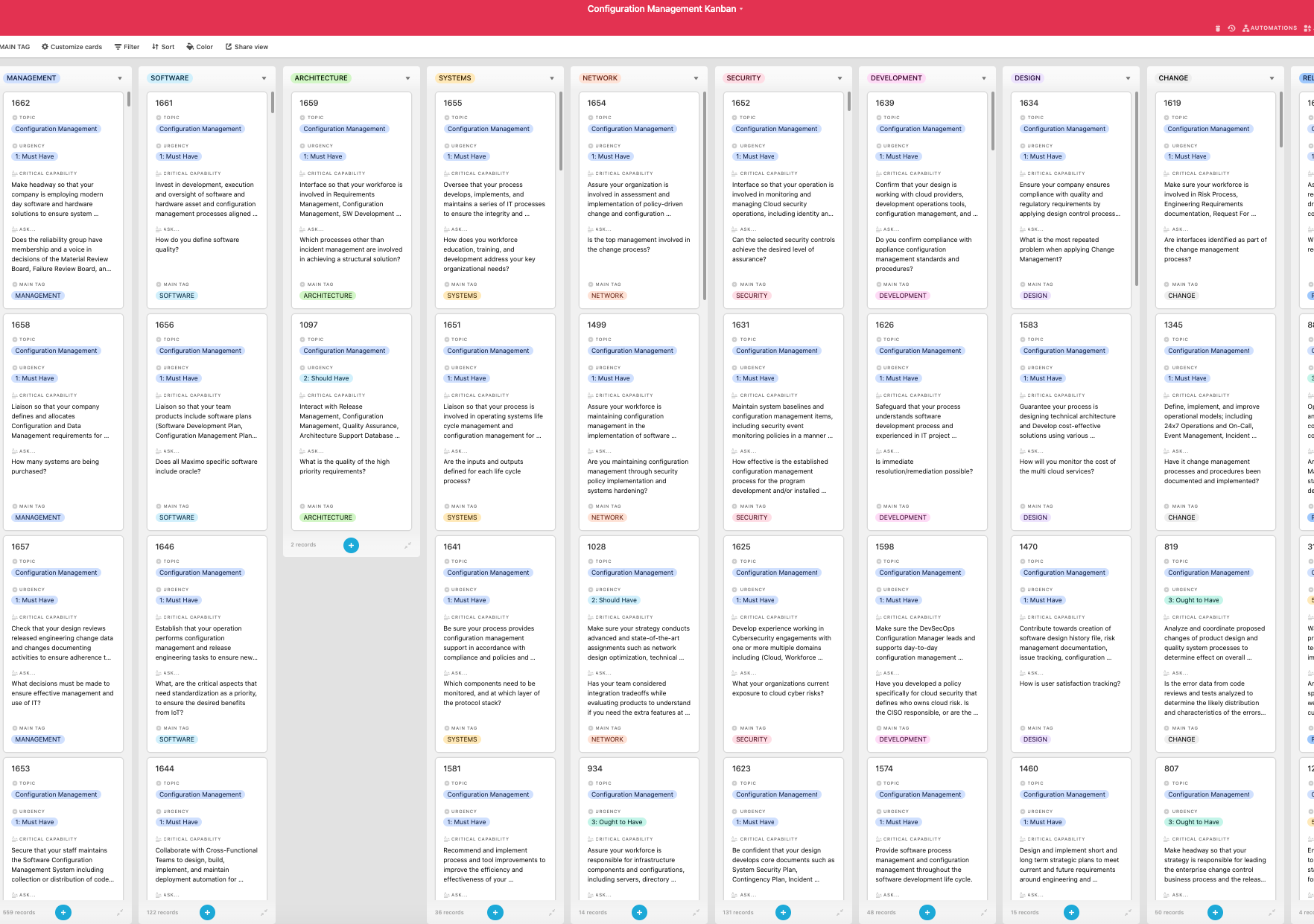
Look inside the Kanban:
https://theartofservice.com/Configuration-Management-kanban
Make headway so that your company is employing modern day software and hardware solutions to ensure system reliability, redundancy, sustainability, security compliance, and (internal) customer satisfaction; utilizing system engineering methods and standards such as traceability, system verification, system validation, baseline descriptions, configuration management and change control to develop first time quality system that is operable and maintainable.
Benefits of the Configuration Management Kanban
- How does software configuration management facilitate the changes that occur during various stages of a system development life cycle in your organization?
- What Enterprise Content Management processes and supporting software tools does your organization use?
- To what degree have information system configuration management policies and procedures been defined and implemented across your organization?
- Does your organization have a documented effective configuration management and change management process defined?
- Do you have an effective configuration management process in place for system software?
- Are change control/ configuration management procedures followed for all software and hardware modifications of systems that process and store sensitive information?
- Does your organization have formalized processes for IT support services, problem management, change management and configuration management?
- For major system acquisitions and major projects, does the project office include a configuration management plan as a component of the project management plan?
- Is a configuration management process in place that controls access to all software code and hardware components throughout the system lifecycle?
- How much visibility does a client have into your internal processes, including Software Quality Assurance (SQA) activities, configuration management and testing?
Summary
The Art of Service has identified and prioritized 1662 Configuration Management critical capabilities and use cases to assess and use. Leaders can select those results that best align with their business needs before implementing a solution.
The Art of Service's Critical Capabilities evaluates and prioritizes hundreds of results to help with the outcome selection process.
This Critical Capabilities Kanban will enable leaders to shortlist hundreds of appropriate results fast, because they are uniquely ready-to-use prioritized, starting with the 'Must Have' category; the most urgent and critical priorities.
This Kanban will help you plan and manage your Configuration Management roadmap.
- Transform the data into actionable views for your organization: business data changes, so how you view it should be flexible. Create the perfect view that's right for you.
- Put your workflows on autopilot: Help your team go faster and focus on what matters by automating your processes. Upload and use the Kanban with your favorite apps and services like Asana, Airtable, Basecamp, Monday.com, Atlassian, Trello etc.
- Knock down data silos: Align your teams around a single source of truth with real-time data from different sources. Point. Click. Stay in Sync.
- Use it's flexible reporting for your unique use case: Whether you're "no-code" or you "know-code", the Kanban is the foundational tool to show what you want to who needs to see it.
Included in your instant download purchase are the following digital products:
As seen in the Kanban above, the complete 1662 Configuration Management critical capabilities and use cases, their prioritization, workflows, tagging and questions.
The download is available as an easy to re-use Excel format, which you can use as is, or import in any management tool of your choice, like Monday.com, Atlassian, Smartsheet, Power BI, Asana, Airtable etc.
Also included is the Configuration Management critical capabilities Book in PDF format covering all the criteria including ideas for (potential) roles to assign the criteria to. Table of contents:
About The Art of Service
Configuration Management Critical Capabilities, Meaningful Metrics And Their Prioritization
Background
Prioritization Of Requirements
The Prioritization Categories Are:
- Must Have
- Should Have
- Ought to Have
- Might Have
- Could Have
Use In New Product/Service/Process Development
Benefits
The Critical Configuration Management Capabilities And Their Priorities:
- Priority - Must Have #
- Priority - Should Have #
- Priority - Ought to Have #
- Priority - Might Have #
- Priority - Could Have #
Index
You're in good company. Join:
Trusted by: BAE Systems, Falconwood, Inc., BDO, University of Arizona Global Campus, LOCKHEED MARTIN CORPORATION, Amgen, Ameresco, Deloitte, Blend, Peraton, Serry Systems, Singer Vehicle Design, TENICA and Associates LLC, Austin Transit Partnership, Gryphon Technologies, Thales Group, UnitedHealth Group, Nielsen, Nitor, Bristol Myers Squibb, Liberty University, Anne Arundel County, MD, National Security Agency, Icore Infotech, Amazon Web Services, Inc., L B & B ASSOCIATES INC, Jovian Concepts, Blue Cross Blue Shield of Massachusetts, Criterion Systems, Inc., MAXIMUS, CyOne, Inc., UC San Diego, Vickers & Nolan Enterprises, General Dynamics Mission Systems, Inc, BOEING, PNC Financial Services Group, Raytheon Intelligence & Space, Mlt Systems, LightGrid, US Department of the Navy - Agency Wide, Technology, Automation, and Management, Inc., NJ Office of Homeland Security & Preparedness, CENCORE LLC, PTC Inc., Penn State University, US National Institutes of Health, Amentum, Oklahoma State University, General Dynamics Information Technology, Avening Management and Technical Services, Zachary Piper Solutions, NCC Group, Jacobs, ARMR Solutions, GAMA-1 Technologies, Versant Health, Ironclad Technnology Services, NCI Information Systems Inc., US Department of State - Agency Wide, US Defense Information Systems Agency, Wellmark Blue Cross and Blue Shield, US Geological Survey, US Government Accountability Office, KeyLogic Systems, AMCHealth, U.S. Army Cyber Command, Microsoft, Applied Information Sciences, Pfizer, US Air Force Services Agency, US National Security Agency/Central Security Service, US Bureau of Engraving and Printing, Bauer Technologies, Inc, QVine Corporation, US Defense Threat Reduction Agency, SAIC, ArcBest, Axiologic Solutions, CTFV, IHG, IntelliGenesis, LLC, Evans & Chambers Technology, Ideal Innovations, Inc, Nike, Cruise