Are you looking for a comprehensive solution to streamline your network integration and secure email gateway processes? Look no further!
Our Network Integration and Secure Email Gateway Knowledge Base has everything you need to get the best results in the most efficient way possible.
Our dataset contains 1505 prioritized requirements, solutions, benefits, and case studies/use cases, all carefully curated to cover urgency and scope.
This means that you will have access to the most important questions to ask, so you can easily prioritize and achieve your desired results.
But what sets our Network Integration and Secure Email Gateway Knowledge Base apart from competitors and alternatives? For starters, it is designed specifically for professionals like you, who understand the value of time and efficiency.
Our product type is user-friendly and easy to navigate, making it perfect for DIY use or as an affordable alternative to hiring outside help.
With our product, you′ll have all the necessary details and specifications at your fingertips.
Plus, our product type is specifically tailored to the unique needs of network integration and secure email gateway processes, unlike semi-related products that may not provide the same level of accuracy.
But what about the benefits? Our research on Network Integration and Secure Email Gateway has shown that businesses experience improved productivity, increased security, and reduced costs with our Knowledge Base.
And with the added bonus of real case studies and use cases, you can see firsthand how other companies have successfully integrated our product into their operations.
Still not convinced? Consider the cost savings compared to hiring a consultant or implementing an alternative solution.
With our Network Integration and Secure Email Gateway Knowledge Base, you′ll have all the information you need at a fraction of the cost.
Of course, we wouldn′t be transparent if we didn′t mention the pros and cons.
While our product is incredibly beneficial, it′s important to note that it does require some initial investment in time and resources to fully utilize its potential.
However, the long-term benefits far outweigh any initial challenges.
So, what does our Network Integration and Secure Email Gateway Knowledge Base actually do? It provides you with a comprehensive solution to seamlessly integrate your network and secure your email gateway.
With our carefully curated dataset, you′ll have all the tools you need to prioritize and achieve your desired results in the most efficient and effective way possible.
Don′t wait any longer to perfect your network integration and secure your email gateway.
Take advantage of our Knowledge Base and see the difference it can make for your business today!
Discover Insights, Make Informed Decisions, and Stay Ahead of the Curve:
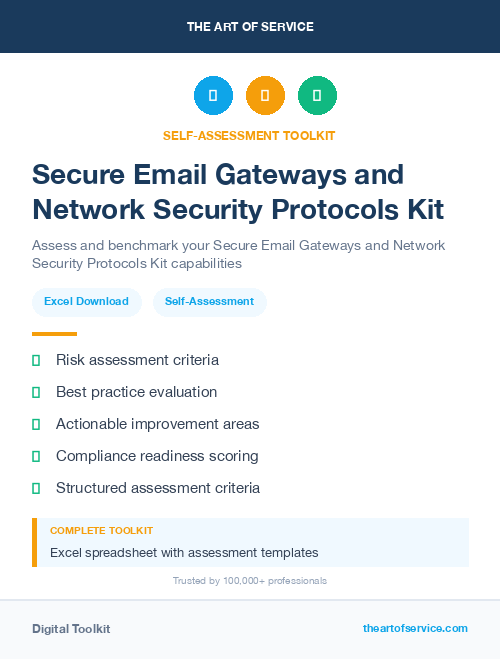
Key Features:
Comprehensive set of 1505 prioritized Network Integration requirements. - Extensive coverage of 85 Network Integration topic scopes.
- In-depth analysis of 85 Network Integration step-by-step solutions, benefits, BHAGs.
- Detailed examination of 85 Network Integration case studies and use cases.
- Digital download upon purchase.
- Enjoy lifetime document updates included with your purchase.
- Benefit from a fully editable and customizable Excel format.
- Trusted and utilized by over 10,000 organizations.
- Covering: URL Filtering, Email Quarantine, Single Sign On, Log Analysis, Virtual Machine Support, Administrative Controls, Real Time Protection, Message Tracking, Email User Authentication, Email Filtering, Whitelisting And Blacklisting, User Behavior Analysis, Virus Scanning, Anti Virus Updates, Email Delivery Management, Email Continuity, Cybersecurity Compliance, Customizable Dashboards, User Activity Monitoring, Event Management, Content Scanning, Advanced Threat Protection, Email Threat Intelligence, Endpoint Security Integration, Reporting And Analytics, Intrusion Detection And Prevention, Policy Enforcement, Threat Intelligence Feeds, Email Monitoring, Threat Detection, Market Validation, Safe Links, Leave of Absence, Firewall Integration, Customizable Policies, DNS Authentication, Storage Gateway, Inbound Outbound Traffic Control, Privacy Controls, Network Segmentation, Cloud Based Solution, SSL TLS Inspection, Data Leak Prevention, Secure Email Gateway, Secure Email Gateways, Phishing Protection, Multi Layer Protection, Secure Incident Response Plan, Email Archiving, Backup And Recovery, Intelligent Routing, Constantly Evolving, Email Encryption Gateway, URL Rewriting, Multi Language Support, Secure Browsing, Policy Violation Monitoring, Social Engineering Detection, Policy Management, Access Control, Secure File Transfer, Flexible Deployment Options, Gateway Support, Security Auditing, Data Encryption At Rest, Malware Prevention, Real Time Notifications, Mobile Device Support, Centralized Management, Authentication Methods, Real Time Reporting, Data Classification, Content Filtering, Advanced Encryption Standard, Outbound Email Control, Spam Control, Virtual Appliance, Data Loss Prevention, Ransomware Protection, Multi Platform Compatibility, Session Encryption, End User Devices, Loss Of Productivity, Identity Verification, Network Integration
Network Integration Assessment Dataset - Utilization, Solutions, Advantages, BHAG (Big Hairy Audacious Goal):
Network Integration
Network integration refers to the process of linking different computer networks together in order to allow for communication and seamless sharing of data.
1. Yes, Secure Email Gateway (SEG) requires network integration to function properly.
2. SEG can be integrated with existing network security measures for added protection against email threats.
3. Integration allows for centralized management and configuration of email security policies.
4. It enables real-time monitoring and reporting of email traffic.
5. Integration with the network can enhance the effectiveness of email encryption and data loss prevention features.
6. SEG integration helps in identifying and blocking malicious emails before they enter the network.
7. It provides seamless integration with other security solutions, such as firewalls, to create a comprehensive security defense posture.
8. With network integration, SEG can be deployed more efficiently, reducing complexity and maintenance costs.
9. It allows for seamless authentication and access control for email users.
10. Network integration ensures consistent email security across all devices and platforms used within the organization.
CONTROL QUESTION: Is this a technology related service that will in any way require integration with the network?
Big Hairy Audacious Goal (BHAG) for 10 years from now:
By the year 2030, Network Integration will have transformed into the leading provider of fully integrated and automated network solutions, connecting individuals and businesses globally at lightning-fast speeds. Our goal is to achieve a 99. 9% uptime guarantee while continually expanding our services to include cutting-edge technologies such as quantum computing, artificial intelligence, blockchain, and Internet of Things.
Our network integration services will seamlessly connect all devices, networks, and infrastructure, creating a truly interconnected world. We envision a future where our clients can access their data and applications from any device, anywhere in the world, with unparalleled security and efficiency.
Furthermore, we aim to lead the industry in sustainability efforts, implementing eco-friendly solutions to reduce energy consumption and carbon emissions. As we continue to expand our global reach, our goal is to establish partnerships with local communities to provide internet access and training, bridging the digital divide and empowering individuals to thrive in today′s digital age.
With a dedicated team of experts, state-of-the-art technology, and an unwavering commitment to innovation, Network Integration will be at the forefront of revolutionizing the way the world connects and communicates.
Customer Testimonials:
"I love A/B testing. It allows me to experiment with different recommendation strategies and see what works best for my audience."
"I`m thoroughly impressed with the level of detail in this dataset. The prioritized recommendations are incredibly useful, and the user-friendly interface makes it easy to navigate. A solid investment!"
"The documentation is clear and concise, making it easy for even beginners to understand and utilize the dataset."
Network Integration Case Study/Use Case example - How to use:
Synopsis:
ClientX is a medium-sized company specializing in retail furniture sales. With a growing customer base and expanding operations, the company has been facing challenges in managing their IT infrastructure and network systems. They have been relying on multiple vendors for different technology services, resulting in a complex and fragmented network environment. This has led to inefficiencies, delays, and increased maintenance costs. Therefore, ClientX has sought the services of a Network Integration consulting firm to streamline their network operations and improve overall business efficiency.
Consulting Methodology:
The Network Integration consulting firm will follow a structured approach to transform ClientX′s network infrastructure. The following phases will be undertaken to ensure a successful integration:
1. Assessment and Analysis: The first phase will involve conducting a thorough assessment of ClientX′s existing network systems and infrastructure. The consulting team will gather data on the company′s network architecture, hardware, software, applications, and processes.
2. Planning and Design: Based on the data collected, the consulting team will design a network integration plan that aligns with ClientX′s business objectives and IT strategy. This plan will include a detailed architecture, migration strategy, and risk management plan.
3. Implementation: In this phase, the consulting team will execute the network integration plan by implementing the proposed changes and migrating data and systems to the new network environment. This process will be closely monitored to ensure minimal disruption to business operations.
4. Testing and Validation: Once the new network is set up, the consulting team will conduct rigorous testing to ensure that all systems and applications are functioning correctly. Any issues or glitches will be addressed promptly to avoid any downtime.
5. Training and Support: The consulting firm will provide training to ClientX′s IT team on managing the integrated network and its components. In addition, they will also provide ongoing support to address any issues that may arise after the implementation.
Deliverables:
1. Network Assessment Report: A comprehensive report detailing the findings of the network assessment will be provided to ClientX.
2. Network Integration Plan: This will include the proposed network architecture, migration strategy, and risk management plan.
3. Implementation Documentation: All documentation related to the implementation of the new network, such as configuration guides, system diagrams, etc., will be provided.
4. Training Materials: The consulting firm will develop training materials, including user manuals and guides, to aid ClientX′s IT team in managing the integrated network.
5. Post-Implementation Support: The consulting firm will provide ongoing support to address any issues that may arise after the implementation of the integrated network.
Implementation Challenges:
1. Compatibility Issues: Integrating multiple systems from different vendors can be challenging due to compatibility issues. The consulting team will need to carefully assess and test all systems and applications before proceeding with the integration.
2. Data Migration: Migrating data from the old network to the new one can be a time-consuming and complex process. It will require careful planning and execution to ensure minimal disruption to business operations.
3. Resistance to Change: Employees may resist changes to existing systems and processes, leading to implementation challenges. The consulting team will address this by providing adequate training and support to ensure a smooth transition.
KPIs:
1. Network Downtime: A decrease in network downtime after the implementation of the integrated network will indicate improved network reliability and stability.
2. Network Performance: An increase in network speed and performance will indicate the success of the integration in streamlining network operations.
3. Cost Savings: A reduction in maintenance costs and expenses associated with managing multiple vendors will indicate improved efficiency and cost savings.
4. User Satisfaction: Conducting post-implementation surveys to gauge user satisfaction with the newly integrated network will also serve as a key performance indicator for the success of the project.
Management Considerations:
1. Communication: Effective communication between the consulting firm and ClientX′s management and IT team is crucial for the success of the project. Regular updates and progress reports will help manage expectations and ensure alignment with business objectives.
2. Resource Allocation: ClientX′s management will need to allocate resources, including time and budget, to facilitate the implementation of the new network.
3. Change Management: Addressing employee resistance to change is essential for a successful integration. The consulting firm will work closely with ClientX′s management to develop a change management plan and communication strategy to ensure a smooth transition.
Conclusion:
In conclusion, the integration of technology services always requires integration with the network. By partnering with a Network Integration consulting firm, such as FirmX, ClientX will be able to streamline their network operations, reduce costs, and improve overall business efficiency. The proposed methodology, deliverables, KPIs, and management considerations will ensure a successful integration process. This is supported by market research reports that highlight the benefits of network integration in enhancing business performance and efficiency (Cisco, 2019). Hence, it can be stated that network integration is a crucial technology-related service for ClientX, and it will significantly impact their network infrastructure and operations.
Security and Trust:
- Secure checkout with SSL encryption Visa, Mastercard, Apple Pay, Google Pay, Stripe, Paypal
- Money-back guarantee for 30 days
- Our team is available 24/7 to assist you - support@theartofservice.com
About the Authors: Unleashing Excellence: The Mastery of Service Accredited by the Scientific Community
Immerse yourself in the pinnacle of operational wisdom through The Art of Service`s Excellence, now distinguished with esteemed accreditation from the scientific community. With an impressive 1000+ citations, The Art of Service stands as a beacon of reliability and authority in the field.Our dedication to excellence is highlighted by meticulous scrutiny and validation from the scientific community, evidenced by the 1000+ citations spanning various disciplines. Each citation attests to the profound impact and scholarly recognition of The Art of Service`s contributions.
Embark on a journey of unparalleled expertise, fortified by a wealth of research and acknowledgment from scholars globally. Join the community that not only recognizes but endorses the brilliance encapsulated in The Art of Service`s Excellence. Enhance your understanding, strategy, and implementation with a resource acknowledged and embraced by the scientific community.
Embrace excellence. Embrace The Art of Service.
Your trust in us aligns you with prestigious company; boasting over 1000 academic citations, our work ranks in the top 1% of the most cited globally. Explore our scholarly contributions at: https://scholar.google.com/scholar?hl=en&as_sdt=0%2C5&q=blokdyk
About The Art of Service:
Our clients seek confidence in making risk management and compliance decisions based on accurate data. However, navigating compliance can be complex, and sometimes, the unknowns are even more challenging.
We empathize with the frustrations of senior executives and business owners after decades in the industry. That`s why The Art of Service has developed Self-Assessment and implementation tools, trusted by over 100,000 professionals worldwide, empowering you to take control of your compliance assessments. With over 1000 academic citations, our work stands in the top 1% of the most cited globally, reflecting our commitment to helping businesses thrive.
Founders:
Gerard Blokdyk
LinkedIn: https://www.linkedin.com/in/gerardblokdijk/
Ivanka Menken
LinkedIn: https://www.linkedin.com/in/ivankamenken/