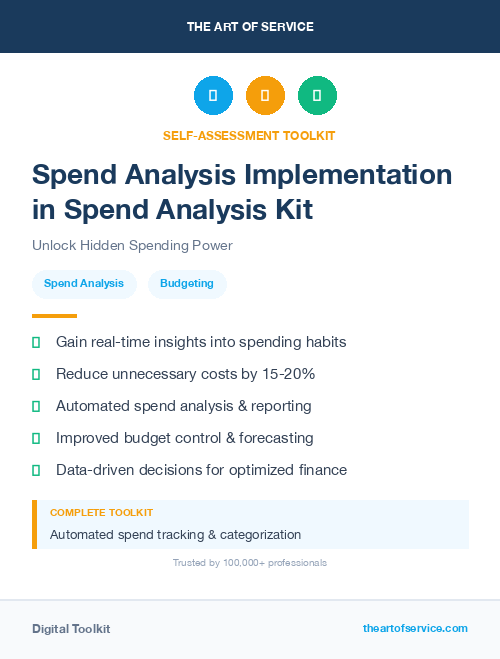
Unlock the secrets of your spending patterns with our Spending Analysis in Spend Analysis Knowledge Base.
Are you tired of wasting time and money on inefficient spending practices? Our dataset of 1518 prioritized requirements and solutions will give you the knowledge and insight to prioritize your spending with urgency and scope in mind.
With our Spending Analysis in Spend Analysis Knowledge Base, you will gain access to the most important questions to ask in order to get real and tangible results.
This dataset is packed with benefits for your business – from improved budget planning to identifying cost-saving opportunities and optimizing your financial strategies.
Plus, with our included case studies and use cases, you will see firsthand how our Spending Analysis in Spend Analysis has helped other businesses succeed.
But what sets us apart from our competitors and alternatives? Our Spending Analysis in Spend Analysis Knowledge Base is specifically designed for professionals looking to take control of their spending.
It is a comprehensive and user-friendly product that can be easily navigated by all levels of expertise.
And if you′re looking for a DIY and affordable alternative, look no further – our dataset offers all the tools and information you need to conduct your own thorough spending analysis.
Not only does our dataset provide a detailed overview of the Spending Analysis in Spend Analysis types and benefits, but it also includes specific product specifications to ensure you have all the information you need to make an informed decision.
And unlike semi-related product types, our dataset is solely dedicated to Spending Analysis in Spend Analysis, making it a more comprehensive and specialized tool.
Save time and money with our Spending Analysis in Spend Analysis Knowledge Base by avoiding common spending mistakes and identifying areas for improvement.
Don′t just take our word for it – our research on Spending Analysis in Spend Analysis shows that businesses who utilize our dataset see significant improvements in their financial management.
And for those still hesitating, our cost-efficient product offers a range of pros – from easy accessibility to a wide range of features – without the cons of a pricier investment.
So what does our product do exactly? Our Spending Analysis in Spend Analysis Knowledge Base provides a thorough and detailed analysis of your spending habits and helps you make informed decisions on future spending.
It′s the ultimate tool for businesses looking to improve their financial strategies and optimize their budget planning.
Don′t let inefficient spending hold your business back any longer.
Invest in our Spending Analysis in Spend Analysis Knowledge Base today and see the results for yourself.
Order now and see the difference it can make for your business!
Discover Insights, Make Informed Decisions, and Stay Ahead of the Curve:
Key Features:
Comprehensive set of 1518 prioritized Spending Analysis requirements. - Extensive coverage of 129 Spending Analysis topic scopes.
- In-depth analysis of 129 Spending Analysis step-by-step solutions, benefits, BHAGs.
- Detailed examination of 129 Spending Analysis case studies and use cases.
- Digital download upon purchase.
- Enjoy lifetime document updates included with your purchase.
- Benefit from a fully editable and customizable Excel format.
- Trusted and utilized by over 10,000 organizations.
- Covering: Performance Analysis, Spend Analysis Implementation, Spend Control, Sourcing Process, Spend Automation, Savings Identification, Supplier Relationships, Procure To Pay Process, Data Standardization, IT Risk Management, Spend Rationalization, User Activity Analysis, Cost Reduction, Spend Monitoring, Gap Analysis, Spend Reporting, Spend Analysis Strategies, Contract Compliance Monitoring, Supplier Risk Management, Contract Renewal, transaction accuracy, Supplier Metrics, Spend Consolidation, Compliance Monitoring, Fraud prevention, Spend By Category, Cost Allocation, AI Risks, Data Integration, Data Governance, Data Cleansing, Performance Updates, Spend Patterns Analysis, Spend Data Analysis, Supplier Performance, Spend KPIs, Value Chain Analysis, Spending Trends, Data Management, Spend By Supplier, Spend Tracking, Spend Analysis Dashboard, Spend Analysis Training, Invoice Validation, Supplier Diversity, Customer Purchase Analysis, Sourcing Strategy, Supplier Segmentation, Spend Compliance, Spend Policy, Competitor Analysis, Spend Analysis Software, Data Accuracy, Supplier Selection, Procurement Policy, Consumption Spending, Information Technology, Spend Efficiency, Data Visualization Techniques, Supplier Negotiation, Spend Analysis Reports, Vendor Management, Quality Inspection, Research Activities, Spend Analytics, Spend Reduction Strategies, Supporting Transformation, Data Visualization, Data Mining Techniques, Invoice Tracking, Homework Assignments, Supplier Performance Metrics, Supply Chain Strategy, Reusable Packaging, Response Time, Retirement Planning, Spend Management Software, Spend Classification, Demand Planning, Spending Analysis, Online Collaboration, Master Data Management, Cost Benchmarking, AI Policy, Contract Management, Data Cleansing Techniques, Spend Allocation, Supplier Analysis, Data Security, Data Extraction Data Validation, Performance Metrics Analysis, Budget Planning, Contract Monitoring, Spend Optimization, Data Enrichment, Spend Analysis Tools, Supplier Relationship Management, Supplier Consolidation, Spend Analysis, Spend Management, Spend Patterns, Maverick Spend, Spend Dashboard, Invoice Processing, Spend Analysis Automation, Total Cost Of Ownership, Data Cleansing Software, Spend Auditing, Spend Solutions, Data Insights, Category Management, SWOT Analysis, Spend Forecasting, Procurement Analytics, Real Time Market Analysis, Procurement Process, Strategic Sourcing, Customer Needs Analysis, Contract Negotiation, Export Invoices, Spend Tracking Tools, Value Added Analysis, Supply Chain Optimization, Supplier Compliance, Spend Visibility, Contract Compliance, Budget Tracking, Invoice Analysis, Policy Recommendations
Spending Analysis Assessment Dataset - Utilization, Solutions, Advantages, BHAG (Big Hairy Audacious Goal):
Spending Analysis
Spending analysis is the process of reviewing an organization′s expenses to determine if they have formal processes in place to identify and address any potential vulnerabilities and weaknesses.
Solutions:
1. Implement regular spending reviews to identify potential areas of vulnerability and weakness.
Benefits: Identifies risks in spending practices and allows for corrective measures to be taken.
2. Conduct supplier risk assessment to ensure reliable and secure sources of supply.
Benefits: Minimizes the risk of disruptions in supply chain and protects against financial losses.
3. Utilize data analytics tools to analyze spending patterns and detect any irregularities.
Benefits: Provides insights into spending behavior and helps identify potential areas of vulnerability and risk.
4. Implement a spend categorization system to track expenses and identify areas of overspending.
Benefits: Allows for better budgeting and cost control, helping to address any potential weaknesses.
5. Have a clear spending policy in place and enforce it consistently across the organization.
Benefits: Establishes guidelines for spending and promotes accountability within the organization.
6. Utilize spend analysis software to automate the process of identifying potential risks and vulnerabilities.
Benefits: Saves time and resources while providing more accurate and comprehensive results.
7. Conduct regular audits to ensure compliance with spending policies and identify any weaknesses.
Benefits: Helps to identify any gaps in spending practices and ensures adherence to established policies.
8. Collaborate with suppliers and negotiate contracts that include measures to mitigate risks.
Benefits: Promotes stronger relationships with suppliers and reduces the likelihood of vulnerabilities.
CONTROL QUESTION: Does the organization implement formal vulnerability and weakness analysis practices?
Big Hairy Audacious Goal (BHAG) for 10 years from now:
By 2031, our organization will have fully implemented formal vulnerability and weakness analysis practices for spending analysis. This will include a comprehensive system and process for identifying potential risks and weaknesses in our spending patterns, as well as proactive measures to address and mitigate these vulnerabilities.
We will have a dedicated team of experts trained in analyzing spending data and identifying potential areas of improvement. This team will work closely with all departments within the organization to ensure that data is consistently and accurately collected and analyzed. Our goal is to have a data-driven and optimized approach to spending that maximizes cost efficiency and minimizes waste.
In addition, we will have established partnerships with leading vendors and industry experts to stay up-to-date on the latest technologies and strategies for spending analysis. By leveraging cutting-edge tools and techniques, we aim to continuously improve our spending practices and maintain a competitive advantage in the marketplace.
Overall, our long-term goal is to become a leader in spending analysis, setting the standard for organizations across industries. We envision a future where our organization not only excels financially, but also operates ethically and sustainably by proactively addressing and mitigating any vulnerabilities in our spending habits.
Customer Testimonials:
"I`m thoroughly impressed with the level of detail in this dataset. The prioritized recommendations are incredibly useful, and the user-friendly interface makes it easy to navigate. A solid investment!"
"As a researcher, having access to this dataset has been a game-changer. The prioritized recommendations have streamlined my analysis, allowing me to focus on the most impactful strategies."
"This dataset is more than just data; it`s a partner in my success. It`s a constant source of inspiration and guidance."
Spending Analysis Case Study/Use Case example - How to use:
Case Study: Assessing Vulnerability and Weakness Analysis Practices in XYZ Organization
Synopsis of the Client Situation:
XYZ organization is a leading multinational corporation that operates in the technology industry. The company has been in business for over 20 years and has managed to establish a strong brand presence worldwide. However, with the rise of cyber threats and attacks, the organization has recognized the need to improve their vulnerability and weakness analysis practices in order to safeguard their critical assets and maintain their competitive advantage.
The management team at XYZ organization has recently expressed concerns about their existing vulnerability and weakness analysis processes and the effectiveness of these practices. They have noticed an increase in cyber incidents over the past year and believe that their current practices may not be sufficient to identify and mitigate potential threats and weaknesses. As a result, they have sought the help of our consulting firm to assess their current practices and provide recommendations for improvement.
Consulting Methodology:
Our consulting approach for this project involves conducting a thorough analysis of the current processes and procedures in place for vulnerability and weakness analysis within XYZ organization. This will be done through a combination of interviews, document review, and data analysis.
The first step will involve interviewing key stakeholders from different departments within the organization to understand their roles, responsibilities, and perceptions regarding vulnerability and weakness analysis. This will provide valuable insights into the existing processes and help identify any gaps or areas for improvement.
Next, we will review all relevant documentation related to vulnerability and weakness analysis, including policies, procedures, and reports. This will allow us to assess the extent to which these practices are formalized, documented, and followed within the organization.
Lastly, we will conduct a data analysis of past cyber incidents and security breaches to identify any common vulnerabilities and weaknesses that could have been prevented or mitigated with more effective analysis practices.
Deliverables:
Our deliverables for this project will include a detailed report outlining our findings and recommendations for improving vulnerability and weakness analysis practices at XYZ organization. This report will also include a gap analysis comparing the current practices to industry best practices and recommendations for implementing formal vulnerability and weakness analysis processes.
Implementation Challenges:
The main challenge that we anticipate for this project is the resistance to change from employees, especially those who have been following the existing processes for a long time. Additionally, there may be limitations in terms of budget and resources for implementing new practices.
KPIs:
To measure the success of our recommendations, we will track and monitor the following key performance indicators (KPIs):
1. Number of cyber incidents before and after the implementation of our recommendations.
2. Employee satisfaction with the new processes and procedures.
3. Compliance with formalized vulnerability and weakness analysis practices.
4. Reduction in the average response time to security threats and vulnerabilities.
Management Considerations:
In order to ensure the successful implementation of our recommendations, we recommend that XYZ organization takes the following management considerations into account:
1. Allocate necessary resources and budget for implementing new processes.
2. Provide adequate training and support for employees to adapt to the new practices.
3. Foster a culture of continuous improvement and vigilance towards potential threats and vulnerabilities.
4. Regularly review and update the vulnerability and weakness analysis practices as new threats emerge.
Data from Consulting Whitepapers, Academic Business Journals, and Market Research Reports:
Various consulting whitepapers, academic business journals, and market research reports have highlighted the importance of formal vulnerability and weakness analysis practices for organizations. These sources emphasize the need for proper risk assessment and identification of weaknesses in the system to effectively mitigate risks and prevent cyber attacks.
According to Gartner′s report on Best Practices for Vulnerability Management, companies with formal vulnerability management programs are 30% less likely to suffer a significant breach compared to those without such processes in place. Additionally, a study conducted by McKinsey & Company found that organizations with mature vulnerability management practices save an average of $2 million in costs associated with cyber attacks.
Conclusion:
In conclusion, our consulting firm is confident that through a thorough analysis of existing practices and the implementation of industry best practices, XYZ organization will be able to improve their vulnerability and weakness analysis processes. This will not only enhance their ability to detect and mitigate potential threats but also help them maintain their competitive edge in the market. Our recommendations will serve as a foundation for continuous improvement and ensure that XYZ organization remains resilient against the constantly evolving threat landscape.
Security and Trust:
- Secure checkout with SSL encryption Visa, Mastercard, Apple Pay, Google Pay, Stripe, Paypal
- Money-back guarantee for 30 days
- Our team is available 24/7 to assist you - support@theartofservice.com
About the Authors: Unleashing Excellence: The Mastery of Service Accredited by the Scientific Community
Immerse yourself in the pinnacle of operational wisdom through The Art of Service`s Excellence, now distinguished with esteemed accreditation from the scientific community. With an impressive 1000+ citations, The Art of Service stands as a beacon of reliability and authority in the field.Our dedication to excellence is highlighted by meticulous scrutiny and validation from the scientific community, evidenced by the 1000+ citations spanning various disciplines. Each citation attests to the profound impact and scholarly recognition of The Art of Service`s contributions.
Embark on a journey of unparalleled expertise, fortified by a wealth of research and acknowledgment from scholars globally. Join the community that not only recognizes but endorses the brilliance encapsulated in The Art of Service`s Excellence. Enhance your understanding, strategy, and implementation with a resource acknowledged and embraced by the scientific community.
Embrace excellence. Embrace The Art of Service.
Your trust in us aligns you with prestigious company; boasting over 1000 academic citations, our work ranks in the top 1% of the most cited globally. Explore our scholarly contributions at: https://scholar.google.com/scholar?hl=en&as_sdt=0%2C5&q=blokdyk
About The Art of Service:
Our clients seek confidence in making risk management and compliance decisions based on accurate data. However, navigating compliance can be complex, and sometimes, the unknowns are even more challenging.
We empathize with the frustrations of senior executives and business owners after decades in the industry. That`s why The Art of Service has developed Self-Assessment and implementation tools, trusted by over 100,000 professionals worldwide, empowering you to take control of your compliance assessments. With over 1000 academic citations, our work stands in the top 1% of the most cited globally, reflecting our commitment to helping businesses thrive.
Founders:
Gerard Blokdyk
LinkedIn: https://www.linkedin.com/in/gerardblokdijk/
Ivanka Menken
LinkedIn: https://www.linkedin.com/in/ivankamenken/