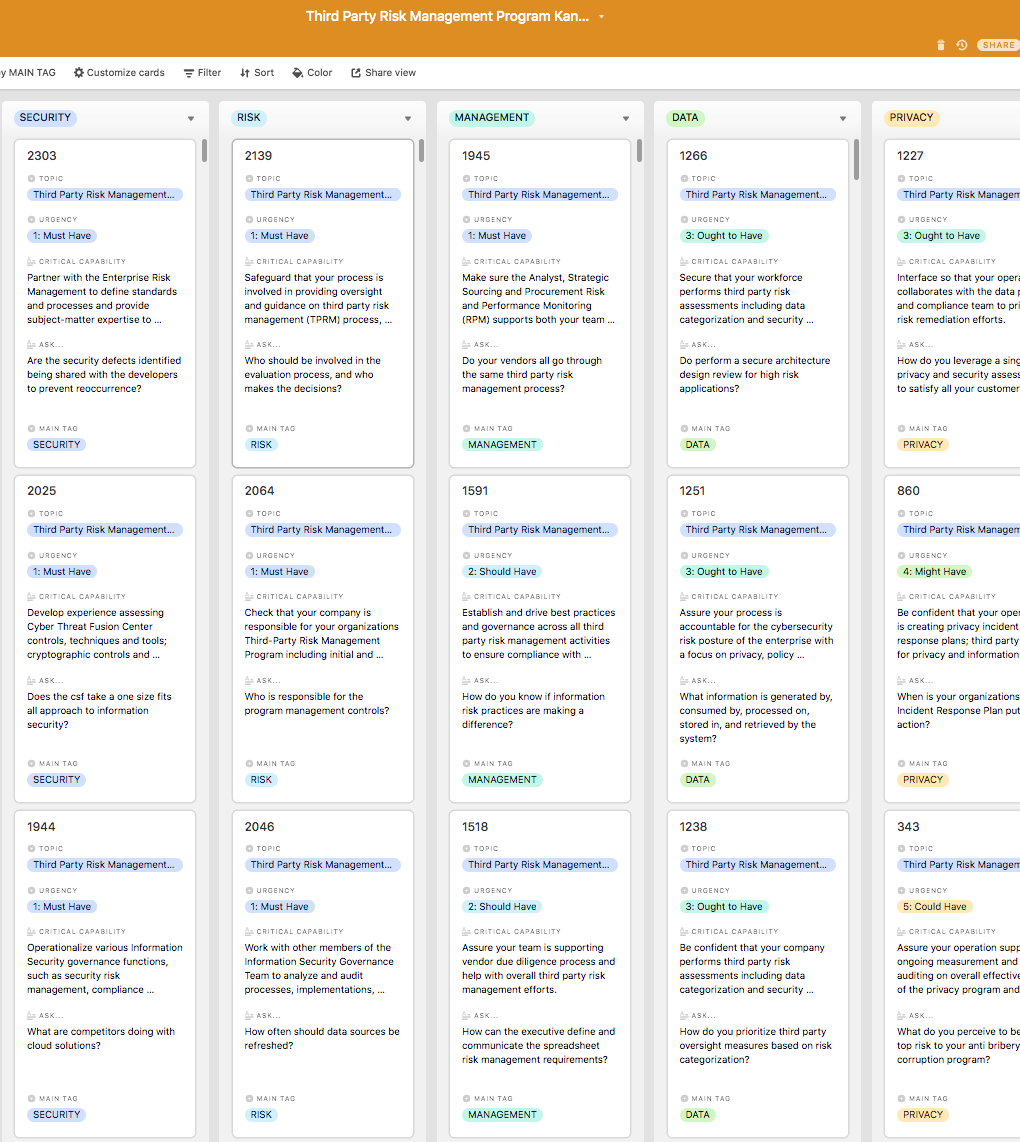
Look inside the Kanban:
https://theartofservice.com/Third-Party-Risk-Management-Program-kanban
Partner with the Enterprise Risk Management to define standards and processes and provide subject-matter expertise to oversee vendor information security risk and inform periodic audits of third-party service providers information security and business continuity controls.
Benefits of the Third Party Risk Management Program Kanban
- Embed risk management into existing business processes.
- Ensure that data will not leak and privacy can be protected.
- Start setting up the right systems that will work securely throughout a potential transaction.
- Ensure that staff will handle the information securely.
- Actively limit the business and legal risks related to non compliance with software licences.
- Ensure vendors have implemented security controls to mitigate third party risks.
- Share information with vendors without being their security standard.
- Ensure that enough partners will invest in security so that all the others will follow suit.
- Evaluate the value and impact to the business if compromised.
- Know if information risk practices are making a difference.
Summary
The Art of Service has identified and prioritized 1946 Third Party Risk Management Program critical capabilities and use cases to assess and use. Leaders can select those results that best align with their business needs before implementing a solution.
The Art of Service's Critical Capabilities evaluates and prioritizes hundreds of results to help with the outcome selection process.
This Critical Capabilities Kanban will enable leaders to shortlist hundreds of appropriate results fast, because they are uniquely ready-to-use prioritized, starting with the 'Must Have' category; the most urgent and critical priorities.
This Kanban will help you plan and manage your Third Party Risk Management Program roadmap.
- Transform the data into actionable views for your organization: business data changes, so how you view it should be flexible. Create the perfect view that's right for you.
- Put your workflows on autopilot: Help your team go faster and focus on what matters by automating your processes. Upload and use the Kanban with your favorite apps and services like Asana, Airtable, Basecamp, Monday.com, Atlassian, Trello etc.
- Knock down data silos: Align your teams around a single source of truth with real-time data from different sources. Point. Click. Stay in Sync.
- Use it's flexible reporting for your unique use case: Whether you're "no-code" or you "know-code", the Kanban is the foundational tool to show what you want to who needs to see it.
Included in your instant download purchase are the following digital products:
As seen in the Kanban above, the complete 1946 Third Party Risk Management Program critical capabilities and use cases, their prioritization, workflows, tagging and questions.
The download is available as an easy to re-use Excel format, which you can use as is, or import in any management tool of your choice, like Monday.com, Atlassian, Smartsheet, Power BI, Asana, Airtable etc.
Also included is the Third Party Risk Management Program critical capabilities Book in PDF format covering all the criteria including ideas for (potential) roles to assign the criteria to. Table of contents:
About The Art of Service
Third Party Risk Management Program Critical Capabilities, Meaningful Metrics And Their Prioritization
Background
Prioritization Of Requirements
The Prioritization Categories Are:
- Must Have
- Should Have
- Ought to Have
- Might Have
- Could Have
Use In New Product/Service/Process Development
Benefits
The Critical Third Party Risk Management Program Capabilities And Their Priorities:
- Priority - Must Have #
- Priority - Should Have #
- Priority - Ought to Have #
- Priority - Might Have #
- Priority - Could Have #
Index
You're in good company. Join:
Trusted by: US Internal Revenue Service, NextEra Energy, Centers for Disease Control and Prevention, Moses Lake Industries, US National Park Service, U.S. Department of State, US Executive Office for U.S. Attorneys and the Office of the U.S. Attorneys, 3M, US Bureau of Reclamation, US Department of the Air Force - Agency Wide, AIG, US Defense Finance and Accounting Service, Aires, PepsiCo, IoXt Alliance, Allegion, Bitdefender, DirectDefense, nVisium, Parker Hannifin Corporation, WWE, DigiCert, Inc., DigiCert, Lawrence Livermore National Laboratory, ITPS, BSI, Ericsson, State of Indiana, Swissbit AG, Lime, PONDURANCE, LLC, Dynamic Motion Control Inc, Microsoft, Ingram Micro, Wind River, Amazon.com Services LLC, Alten, Motorola Solutions, Sensata Technologies, Armis, Signify, AGCO, DMC, Lenovo, Resilience, Ameresco, Check Point Software Technologies Ltd., Fisker Inc, Humulo Engineering, Johns Hopkins Applied Physics Laboratory (APL), Amazon Web Services, Inc., ITmPowered, LEDVANCE, MasterCard, Promega, Plume, Milwaukee Tool, Xage Security, PPL Corporation, Latchable, Matroid, Palo Alto Networks, Leviathan Security, CrowdStrike, Ordr