Look inside the Kanban:
https://theartofservice.com/Threat-Intelligence-kanban
Ensure your team is involved in these the following Information Security programs areas: Endpoint Protection, Risk Management, Threat Management, Incident Management and/or Security Engineering and Operations Support.
Benefits of the Threat Intelligence Kanban
- Does your organization have a cyber threat intelligence program and attack monitoring/alert process?
- What threat intelligence information sharing protocols does your organization use to share and disseminate threat intelligence data?
- How does your organization collect and share threat intelligence that may be useful in mitigating cyber threat risk?
- What security measures does your organization employ to keep your threat intelligence secure?
- How does your organization enrich the data collected with threat intelligence and GeoIP data to enhance the analysis process for higher fidelity and lower false positive alerts?
- What tools does your organization use to receive Cyber Threat Intelligence from other companies?
- How confident are you in the security of sending your organizations threat intelligence data to the cloud for analysis (i.e., log files)?
- What value does threat intelligence bring to your organizations overall security strategy?
- Who is responsible for implementing a threat intelligence program that integrates across your security technologies, teams, and executive cyber risk decisions?
- What sources of cybersecurity threat intelligence does your organization receive?
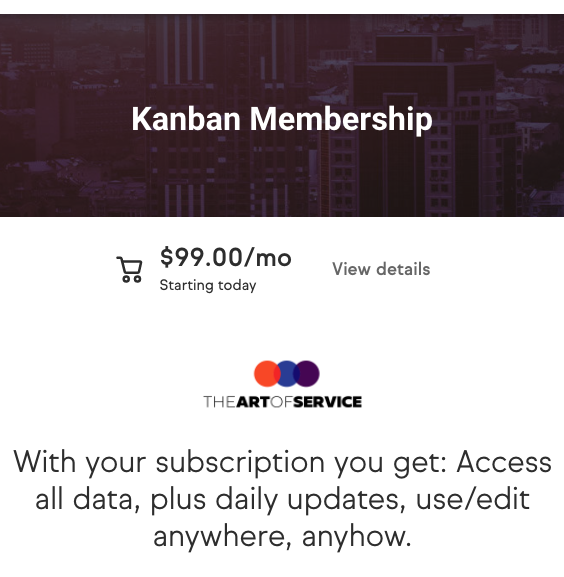
Summary
The Art of Service has identified and prioritized 3387 Threat Intelligence critical capabilities and use cases to assess and use. Leaders can select those results that best align with their business needs before implementing a solution.
The Art of Service's Critical Capabilities evaluates and prioritizes hundreds of results to help with the outcome selection process.
This Critical Capabilities Kanban will enable leaders to shortlist hundreds of appropriate results fast, because they are uniquely ready-to-use prioritized, starting with the 'Must Have' category; the most urgent and critical priorities.
This Kanban will help you plan and manage your Threat Intelligence roadmap.
- Transform the data into actionable views for your organization: business data changes, so how you view it should be flexible. Create the perfect view that's right for you.
- Put your workflows on autopilot: Help your team go faster and focus on what matters by automating your processes. Upload and use the Kanban with your favorite apps and services like Asana, Airtable, Basecamp, Monday.com, Atlassian, Trello etc.
- Knock down data silos: Align your teams around a single source of truth with real-time data from different sources. Point. Click. Stay in Sync.
- Use it's flexible reporting for your unique use case: Whether you're "no-code" or you "know-code", the Kanban is the foundational tool to show what you want to who needs to see it.
Included in your instant download purchase are the following digital products:
As seen in the Kanban above, the complete 3387 Threat Intelligence critical capabilities and use cases, their prioritization, workflows, tagging and questions.
The download is available as an easy to re-use Excel format, which you can use as is, or import in any management tool of your choice, like Monday.com, Atlassian, Smartsheet, Power BI, Asana, Airtable etc.
Also included is the Threat Intelligence critical capabilities Book in PDF format covering all the criteria including ideas for (potential) roles to assign the criteria to. Table of contents:
About The Art of Service
Threat Intelligence Critical Capabilities, Meaningful Metrics And Their Prioritization
Background
Prioritization Of Requirements
The Prioritization Categories Are:
- Must Have
- Should Have
- Ought to Have
- Might Have
- Could Have
Use In New Product/Service/Process Development
Benefits
The Critical Threat Intelligence Capabilities And Their Priorities:
- Priority - Must Have #
- Priority - Should Have #
- Priority - Ought to Have #
- Priority - Might Have #
- Priority - Could Have #
Index
You're in good company. Join:
Trusted by: FREEDOM CONSULTING GROUP, McKinsey & Company, DataLink Fund Solutions, Huntington Ingalls Industries Inc., Raytheon Intelligence & Space, Northrop Grumman, Major League Baseball, PRICE WATERHOUSE COOPERS, Booz Allen Hamilton, PepsiCo, Foot Locker, Home Depot / THD, Tanium, Intel, IBM, NATIONAL GRID CO USA (NE POWER), Recorded Future, CrowdStrike, RWJBarnabas Health, Abbott Laboratories, Citi, Honeywell, Splunk, Wipro Limited, LOCKHEED MARTIN CORPORATION, ADP, Hertz, Cardinal Health, TikTok, Microsoft, Proofpoint, IronNet, Information and Infrastructure Technologies, Allegion, Starkey Hearing Technologies, Sandvik, Staff Boom, Seismic, Cielo Talent, LabConnect, LLC, Marriott International, Inc, TrueCommerce, Inc., Pill Club, Siemens, Celestar Corporation, DICK'S Sporting Goods, Alight, Koniag Management Solutions, Kubota Tractor Corp, Clearwater Paper, SiriusXM, Halloran Consulting Group, VMware, Red River Computer Co., Freeport McMoRan, Smiths Medical, Verto Education, George Mason University, Amazon.com Services LLC, Piper Companies, Serry Systems, Loudoun County School District, Ledcor, World Resources Institute, Valiant Solutions, LLC, Oshkosh Corporation, State of Colorado Job Opportunities, Prince George's County, MD, Wells Concrete, BOEING, Travere Therapeutics, Montgomery County Pennsylvania, Critical Solutions, GSK, Abbvie, The Jackson Laboratory, CareFirst BlueCross BlueShield, TYBRAM, The Intellekt Group, GE, Arise Virtual Solutions Inc., UST Global, Michigan Milk Producers Association, Moody Bible Institute, LUXENDO GmbH, Alpha Cloud Partners, NEOSOFT, TDI, Ma'aden Phosphate Company (MPC), Merck, LFB, Pitney Bowes, STS International, Inc., Glanbia Nutritionals, Evolent Health, BeiGene, Bear Robotics, Mitsubishi Motors North America, IDDI, CreativeDrive, Meharry Medical College, Zing Health Holdings Inc, Allegis Global Solutions, IBSS CORP, ADUSA Procurement, DXC, Jushi, Bucknell University, Comcast Spectacor, University of Texas at Dallas, BNY Mellon, Battelle, Kohler, Global Solutions Network Inc, Icon plc, ProSphere, GE Gas Power, CVS Health, Lululemon, Human Security, U.S. Bank, Exelon Corporation, Accenture, LyondellBasell Industries, Iron Vine Security, LLC, Nuspire, LLC