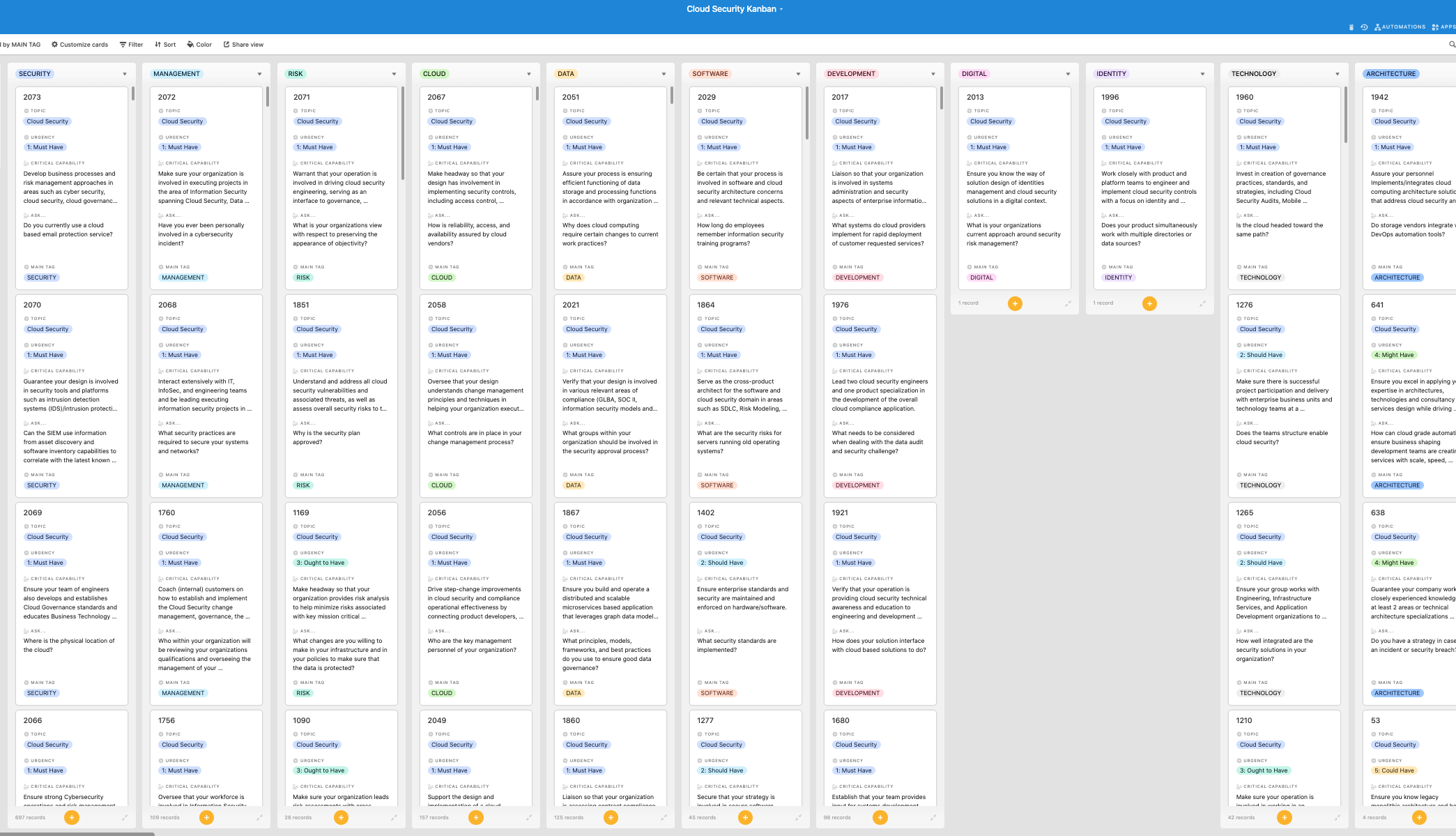
Look inside the Kanban:
https://theartofservice.com/Cloud-Security-kanban
Create a visionary architecture roadmap and organizational strategy to align cloud and security teams with engineering, product management and other business teams.
Benefits of the Cloud Security Kanban
- What cloud services does your organization use and how is your organization sure providers maintain high security standards and robust controls?
- Many cloud providers are expanding big data support with machine learning and other platform as a service options that rely on access to enterprise data. Do you have a full understanding of potential data exposure, compliance, and privacy implications, if the machine learning runs as PaaS inside the providers infrastructure, where provider employees could technically access it, does that create a compliance exposure?
- Does your potential cloud security service provider offer other security services beyond DDoS, or does it only mitigate DDoS attacks?
- Does the cloud service provider have necessary security controls on their human resources?
- What specific security tools does your organization want to use for cloud security monitoring and maintenance?
- How do your data owners merge cloud security data with your organizations own security metrics and policies?
- How does your organization address cloud security concerns using corporate policies and procedures?
- How frequently will a cloud service provider and its cloud services be assessed under your organizations cloud security guidance?
- Does the service meet industry standard cloud security principles as the Cloud Security Alliance, NIST or UK Government Cloud Security Principles and SOC 2?
- Does your organization have a documented cloud security plan or methodology?
Summary
The Art of Service has identified and prioritized 3803 Cloud Security critical capabilities and use cases to assess and use. Leaders can select those results that best align with their business needs before implementing a solution.
The Art of Service's Critical Capabilities evaluates and prioritizes hundreds of results to help with the outcome selection process.
This Critical Capabilities Kanban will enable leaders to shortlist hundreds of appropriate results fast, because they are uniquely ready-to-use prioritized, starting with the 'Must Have' category; the most urgent and critical priorities.
This Kanban will help you plan and manage your Cloud Security roadmap.
- Transform the data into actionable views for your organization: business data changes, so how you view it should be flexible. Create the perfect view that's right for you.
- Put your workflows on autopilot: Help your team go faster and focus on what matters by automating your processes. Upload and use the Kanban with your favorite apps and services like Asana, Airtable, Basecamp, Monday.com, Atlassian, Trello etc.
- Knock down data silos: Align your teams around a single source of truth with real-time data from different sources. Point. Click. Stay in Sync.
- Use it's flexible reporting for your unique use case: Whether you're "no-code" or you "know-code", the Kanban is the foundational tool to show what you want to who needs to see it.
Included in your instant download purchase are the following digital products:
As seen in the Kanban above, the complete 3803 Cloud Security critical capabilities and use cases, their prioritization, workflows, tagging and questions.
The download is available as an easy to re-use Excel format, which you can use as is, or import in any management tool of your choice, like Monday.com, Atlassian, Smartsheet, Power BI, Asana, Airtable etc.
Also included is the Cloud Security critical capabilities Book in PDF format covering all the criteria including ideas for (potential) roles to assign the criteria to. Table of contents:
About The Art of Service
Cloud Security Critical Capabilities, Meaningful Metrics And Their Prioritization
Background
Prioritization Of Requirements
The Prioritization Categories Are:
- Must Have
- Should Have
- Ought to Have
- Might Have
- Could Have
Use In New Product/Service/Process Development
Benefits
The Critical Cloud Security Capabilities And Their Priorities:
- Priority - Must Have #
- Priority - Should Have #
- Priority - Ought to Have #
- Priority - Might Have #
- Priority - Could Have #
Index
You're in good company. Join:
Trusted by: ConvergeOne, IBM, nFrastructure, USAA, Microsoft, Datadog, Wells Fargo, Optiv, Havertys Furniture Companies, Lennox International, Princeton Plasma Physics Laboratory, Oracle, Alexander Technology Group, Triumvirate Environmental, Invesco, Starbucks, Norfolk Southern Corp, II-VI, IT Data Solutions, Cincinnati Children's Hospital, WellSky, Y Soft, Bentley Systems, VMware, NVIDIA, Molina Healthcare, Sedgwick, T. Rowe Price, CrowdStrike, DELUXE CORPORATION, Capital One, CyberArk, Charles Schwab, Farmers Insurance Group, Dell Technologies, Deloitte, Fannie Mae, Avaya, Indeed, Anthem, NJ Transit, Allstate, Aurora, Google, Amazon Web Services, Inc., Apple, KPMG, University of California Santa Cruz, Signify, Mutual of Omaha, Booz Allen Hamilton, Atomic, FireEye, Inc., PRICE WATERHOUSE COOPERS, MasterCard, Spirent Communications, Strategic Technology Partners, TCS, Next Level Impacts, Unisys, Amazon.com Services LLC, Tyson Foods, Inc., Vistra Corporate Services Company, Proofpoint, Coalfire, Capco, Salesforce, Aflac, Incorporated, MetLife, Humana, Secberus, General Mills, Connect Staffing Professional, LLC, Trova, Duke Careers, Pearson, Cruise, Pegasystems, JPMorgan Chase Bank, N.A., BNY Mellon, Forcepoint, Intone Networks, Ortho Clinical Diagnostics, Palo Alto Networks, Morgan Stanley, Citizens, Cognizant Technology Solutions, Connvertex Technologies Inc., HashiCorp, RELX, Rapid7, Western Union, HealthPartners, Tesla, GRSi, Emerson, PepsiCo, HealthStream, Norwegian Cruise Line Holdings Ltd., EPAM Systems, Secureworks, GE Gas Power, LexisNexis Legal & Professional, Veritas Technologies, Praetorian, EY Global Services Limited prod, Vanguard, Independent Financial, Protiviti, IZEA, Radian, Anitian, CAE Inc., NetApp, Postman, Saks Fifth Avenue, Cisco Systems, LendingClub, Capital Markets Gateway, Lazard Ltd., Infoworks.io, BlackRock, The Intellekt Group, 3M, Signet Jewelers, Intel, Armor, FedEx Services, Carilion Clinic, Capgemini, Intercontinental Exchange, Virginia Dept of Social Services, Dremio, Deutsche Bank, BDO, Elastic, Citi, Corning, Vonage, Home Depot / THD, AIR, McDonald's Corporate, Accenture, Kraft Heinz Company, All Turtles, Change Healthcare, Johnson & Johnson Family of Companies, American Equity, firstPRO Inc., Lenovo, Faction, Siemens, OutSystems, Toyota, Appian Corporation, Bucher + Suter, Amcor, Sabel Systems, Aveva, Red Hat Software, Railsbank, Auth0, Hayes | MDaudit, CVS Health, Seagate Technology, Smile CDR Inc., General Dynamics Information Technology, Trek10, SAIC, Cloud Computing Technologies, Turing.Com, iSenpai, Dawson, Blue Cross Blue Shield of Massachusetts, CORMAC, ITR, Slalom Consulting, Cognosante, LLC, Cummins Inc., Envision, Canonical, Cars.com, Tranquil Multi Dynamic Advisory, Savvas Learning Company, Phillips 66, CEDENT, CACI, Computex, Inc., Bank of America, Alight, Egnyte, Splunk, US Consumer Financial Protection Bureau, State Street, Atlis Motor Vehicles, Precise Systems, LMR Staffing, University of Minnesota, Kyndryl, Yakshna Solutions, Sev1Tech, Atlantic Health System, Ingram Micro, Wind River, Alpha Cloud Partners, Bucknell University, Martin Engineering, ERP International, LLC, MindPoint Group, LLC, Publix, RingCentral, McKinsey & Company, Highspot, Papa John's International, Inc., Merck KGaA Darmstadt Germany, Connection, Gartner, Wursta Corporation, Datto Inc., Columbus Global, Catalyte Inc, MATRIX Resources, Splan, Weyerhaeuser, Groviv, Smartronix, Avanade, Berkadia, Wipro Limited, TIAA, Berkley, Experity, Inc, SAP, Makpar Corporation, Hitachi Vantara, Mighty Networks, Baer Group, Maven Wave, Virtustream, PK, NCC Group, EZCORP | EZCORP Inc, Vectra, Rally Health, Infogravity, Abnormal Security, Insight Global, PayNearMe, LOCKHEED MARTIN CORPORATION, Clearcover, Highmark Health, Smart Warehousing, LLC, WALGREENS, Diebold Nixdorf, Snowflake, Thales Group, Zebra Technologies, RealtyMogul, Vivint, Inc., Flatiron Health, Bill.com, Beachbody, SAGE Black Consulting & Contracting LLC, BOK Financial, Peraton, Haverty Furniture Companies, Inc, Auto Club of Southern California, Promega, Kwik Trip Inc, UnitedHealth Group, JLL, Albertsons Companies, Federal Reserve Bank of New York, Brown & Brown Insurance, Papa John's, Octo, Boomi, Novetta, CLEARWATER, Panasonic Corporation of North America, Ensono, Starburst, The Aerospace Corporation, TARGET, WarnerMedia, Highbrow-Tech, Follett Corporation, ALTA IT Services, KMM Technologies, Goldman Sachs, AbleTo, Liferay, Inc., Fidelity Investments, Meredith Corporation, Steampunk, Teladoc Health, OnPrem Solution Partners, Square, Hitachi Vantara Corporation, tunein, Newforma Inc, Semperis, NeuraFlash, Akamai Technologies, Hewlett Packard Enterprise