Are you looking to ensure the highest level of security for your customer′s credit card information? Look no further than our Data Environment in Tool Allow Knowledge Base.
Designed specifically for businesses of all sizes, our knowledge base consists of the most important questions to ask in order to achieve Data Environment.
With urgency and scope in mind, our dataset includes 1557 prioritized requirements, solutions, benefits, results, and example case studies/use cases to guide you through the process.
Why is Data Environment so important? Not only does it protect your customers′ sensitive information, but it also builds trust and credibility for your business.
By following the guidelines outlined in Tool Allow, you can minimize the risk of data breaches and ensure the safety of your customers′ data.
Our knowledge base has been carefully curated by industry experts to provide you with the most comprehensive and up-to-date information on Data Environment.
With our guidance, you can rest assured that your business is meeting all necessary standards and regulations.
Don′t take any chances when it comes to your customers′ data security.
Invest in our Data Environment in Tool Allow Knowledge Base today and enjoy the peace of mind that comes with knowing your business is secure.
Stay ahead of the game and maintain your competitive edge by being one step closer to compliance.
Don′t wait any longer, get started on your journey towards Data Environment now.
Discover Insights, Make Informed Decisions, and Stay Ahead of the Curve:
Key Features:
Comprehensive set of 1557 prioritized Data Environment requirements. - Extensive coverage of 133 Data Environment topic scopes.
- In-depth analysis of 133 Data Environment step-by-step solutions, benefits, BHAGs.
- Detailed examination of 133 Data Environment case studies and use cases.
- Digital download upon purchase.
- Enjoy lifetime document updates included with your purchase.
- Benefit from a fully editable and customizable Excel format.
- Trusted and utilized by over 10,000 organizations.
- Covering: Encryption Standards, Network Security, Data Environment, Privacy Regulations, Data Encryption In Transit, Authentication Mechanisms, Information security threats, Logical Access Control, Information Security Audits, Systems Review, Secure Remote Working, Physical Controls, Vendor Risk Assessments, Home Healthcare, Healthcare Outcomes, Virtual Private Networks, Information Technology, Awareness Programs, Vulnerability Assessments, Incident Volume, Access Control Review, Data Breach Notification Procedures, Port Management, GDPR Compliance, Employee Background Checks, Employee Termination Procedures, Password Management, Social Media Guidelines, Security Incident Response, Insider Threats, BYOD Policies, Healthcare Applications, Security Policies, Backup And Recovery Strategies, Privileged Access Management, Physical Security Audits, Information Security Controls Assessment, Disaster Recovery Plans, Authorization Approval, Physical Security Training, Stimulate Change, Malware Protection, Network Architecture, Compliance Monitoring, Personal Impact, Mobile Device Management, Forensic Investigations, Information Security Risk Assessments, HIPAA Compliance, Data Handling And Disposal, Data Backup Procedures, Incident Response, Home Health Care, Cybersecurity in Healthcare, Data Classification, IT Staffing, Antivirus Software, User Identification, Data Leakage Prevention, Log Management, Online Privacy Policies, Data Breaches, Email Security, Data Loss Prevention, Internet Usage Policies, Breach Notification Procedures, Identity And Access Management, Ransomware Prevention, Security Information And Event Management, Cognitive Biases, Security Education and Training, Business Continuity, Cloud Security Architecture, SOX Compliance, Cloud Security, Social Engineering, Biometric Authentication, Industry Specific Regulations, Mobile Device Security, Wireless Network Security, Asset Inventory, Knowledge Discovery, Data Destruction Methods, Information Security Controls, Third Party Reviews, AI Rules, Data Retention Schedules, Data Transfer Controls, Mobile Device Usage Policies, Remote Access Controls, Emotional Control, IT Governance, Security Training, Risk Management, Security Incident Management, Market Surveillance, Practical Info, Firewall Configurations, Multi Factor Authentication, Disk Encryption, Clear Desk Policy, Threat Modeling, Supplier Security Agreements, Why She, Cryptography Methods, Security Awareness Training, Remote Access Policies, Data Innovation, Emergency Communication Plans, Cyber bullying, Disaster Recovery Testing, Data Infrastructure, Business Continuity Exercise, Regulatory Requirements, Business Associate Agreements, Enterprise Information Security Architecture, Social Awareness, Software Development Security, Penetration Testing, Tool Allow, Secure Coding Practices, Phishing Attacks, Intrusion Detection, Service Level Agreements, Profit with Purpose, Access Controls, Data Privacy, Fiduciary Duties, Privacy Impact Assessments, Compliance Management, Responsible Use, Logistics Integration, Security Incident Coordination
Data Environment Assessment Dataset - Utilization, Solutions, Advantages, BHAG (Big Hairy Audacious Goal):
Data Environment
Data Environment is a set of security standards that businesses must follow to protect customers′ credit card data. Some businesses may see it as a burden, while others view it as an opportunity to improve their organization′s security and reputation.
Solutions:
1. Implementing security controls and processes to comply with PCI DSS
Benefits: Enhances protection of sensitive data, reduces risk of data breaches and protects reputation.
2. Conducting regular vulnerability assessments and penetration testing
Benefits: Helps identify and address potential security weaknesses, keeping systems and data secure and compliant.
3. Regular employee training on data security and handling
Benefits: Educates employees on PCI DSS requirements and promotes a security-conscious culture, reducing risks of human error.
4. Using encryption for data in transit and at rest
Benefits: Protects against unauthorized access to sensitive data, ensuring compliance with PCI DSS requirements.
5. Limiting access to cardholder data on a need-to-know basis
Benefits: Reduces risk of data breaches and ensures compliance with PCI DSS requirements for access control.
6. Regularly monitoring and logging all system activity
Benefits: Helps detect and respond to potential security incidents, and ensures compliance with PCI DSS requirements for logging and auditing.
7. Implementing strong password policies and multi-factor authentication
Benefits: Enhances security of systems and data, and helps meet PCI DSS requirements for access control.
8. Regularly auditing and reporting on compliance status
Benefits: Provides evidence of adherence to PCI DSS requirements, helps identify areas for improvement and maintains compliance.
9. Leveraging third-party security and compliance services
Benefits: Saves time and resources, ensures ongoing compliance with PCI DSS requirements, and provides expert support.
10. Adopting a risk management approach for Data Environment
Benefits: Helps prioritize and address potential risks to cardholder data, leading to more effective compliance efforts.
CONTROL QUESTION: Does the business see Data Environment as the organization enhancement or as a hindrance?
Big Hairy Audacious Goal (BHAG) for 10 years from now:
The big, hairy audacious goal for Data Environment in 10 years is to achieve not just compliance, but full integration and optimization of PCI DSS requirements into the organization′s overall security strategy. This means that Data Environment will no longer be viewed as a separate, burdensome task, but rather as a natural and essential part of the organization′s security framework.
The business will see Data Environment as a crucial enhancement to the organization′s reputation and credibility in the eyes of stakeholders and customers. It will be viewed as a testament to the organization′s commitment to protecting sensitive data and maintaining the highest level of trust with its customers.
Additionally, Data Environment will be seen as a proactive measure that strengthens the organization′s overall security posture and minimizes the risk of costly data breaches. By integrating PCI DSS requirements into the organization′s security strategy, the business will see compliance as a natural and seamless component of their operations, rather than a hindrance.
Ultimately, the organization′s focus on achieving and maintaining Data Environment will lead to increased efficiency, cost savings, and competitive advantage, solidifying its position as a leader in the industry.
Customer Testimonials:
"I`m using the prioritized recommendations to provide better care for my patients. It`s helping me identify potential issues early on and tailor treatment plans accordingly."
"I can`t express how impressed I am with this dataset. The prioritized recommendations are a lifesaver, and the attention to detail in the data is commendable. A fantastic investment for any professional."
"I am impressed with the depth and accuracy of this dataset. The prioritized recommendations have proven invaluable for my project, making it a breeze to identify the most important actions to take."
Data Environment Case Study/Use Case example - How to use:
Case Study: Data Environment - An Organizational Enhancement or Hindrance?
Synopsis of Client Situation:
ABC Corporation is a medium-sized retail company with 50 stores across the United States, specializing in clothing and accessories. The company processes a significant volume of credit card transactions each day, making them subject to the Payment Card Industry Data Security Standard (PCI DSS) compliance. ABC Corporation had recently received multiple warnings from their acquiring bank about their non-compliance with the PCI DSS requirements, which could potentially lead to hefty fines and reputational damage.
The organization′s leadership team was divided on whether to view Data Environment as an enhancement or hindrance. While some believed that it could improve customer trust and strengthen the company′s security posture, others saw it as a burdensome and costly process that would not provide any tangible benefits to the organization. To resolve this dilemma, the company decided to hire a consulting firm to assess their current state of compliance and develop a comprehensive plan for achieving and maintaining Data Environment.
Consulting Methodology:
To address the client′s concerns, our consulting firm utilized a structured approach to assess the organization′s current state of compliance, identify potential gaps, and develop a roadmap for meeting the PCI DSS requirements. The methodology followed a five-step process, including:
1. Initial Assessment: The first step involved conducting an initial assessment to understand the organization′s scope, size, and complexity of its payment card data environment. This initial assessment also helped identify any existing controls and areas that need improvement.
2. Gap Analysis: The next step was to perform a detailed analysis of the organization′s security controls against the PCI DSS requirements. This gap analysis helped identify non-compliant areas and develop remediation steps.
3. Remediation Plan: Based on the results of the gap analysis, a comprehensive remediation plan was developed, outlining the specific tasks and timelines required to achieve compliance.
4. Implementation: The consulting team worked closely with the organization′s IT and security teams to implement the remediation plan. This included configuring new security controls, updating policies and procedures, and conducting employee training.
5. Validation and Reporting: Once the implementation was completed, the consulting firm conducted a final validation assessment to ensure that all PCI DSS requirements were met. A report was then provided to the client, highlighting the achieved compliance level and any remaining gaps.
Deliverables:
The consulting firm provided the following deliverables to ABC Corporation as part of its Data Environment program:
1. Comprehensive assessment report identifying areas of non-compliance and recommended remediation steps.
2. Remediation plan with detailed timelines, tasks, and responsible parties.
3. Updated policies and procedures to align with the PCI DSS requirements.
4. Employee training materials on security awareness, handling of sensitive data, and compliance requirements.
5. Final validation report with the achieved compliance level and recommendations for maintaining compliance in the future.
Implementation Challenges:
During the project, the consulting team faced some common challenges associated with achieving Data Environment. These included:
1. Scope Identification: One of the main challenges was to define the organization′s scope accurately. Due to the widespread use of credit card data across different departments and systems, it was challenging to identify all the touchpoints that needed to be compliant.
2. Resource Constraints: The company had a limited budget and resources allocated for this compliance program, leading to delays in implementing remediation measures and meeting deadlines.
3. Resistance to Change: Some employees were resistant to change and were not convinced of the need for stringent security controls, making it difficult to enforce new policies and procedures.
Key Performance Indicators (KPIs):
To measure the success of the Data Environment program, the following key performance indicators were defined and monitored:
1. Level of Compliance Achieved: The primary KPI was to achieve full compliance with all the PCI DSS requirements.
2. Time to Achieve Compliance: The time taken to reach full compliance was monitored to identify any delays.
3. Percentage of Gaps Closed: The number of identified gaps closed during each phase of implementation was tracked to measure progress and identify areas that required additional attention.
Management Considerations:
To ensure the sustainability of the organization′s compliance efforts, the consulting firm provided the following recommendations to the management team:
1. Regular Training and Awareness Programs: Employees must receive regular training on security best practices and their responsibilities concerning handling sensitive data. This will help enforce a culture of security and minimize the risk of human error.
2. Ongoing Compliance Monitoring: Compliance is not a one-time effort; it must be continuously monitored and maintained. The organization should invest in periodic assessments and gap analyses to identify any new risks or vulnerabilities.
3. Budget Allocation: The organization should allocate a sufficient budget to maintain compliance and address any future changes in the PCI DSS requirements.
Conclusion:
The consulting firm successfully assisted ABC Corporation in achieving full compliance with the PCI DSS requirements. Through the implementation of robust security controls, updated policies and procedures, and employee training, the company was able to mitigate the security risks associated with credit card data processing. As a result, the organization saw an increase in customer trust and satisfaction, leading to a positive impact on its reputation. Moreover, by addressing the compliance concerns, ABC Corporation was able to avoid potential fines and penalties, making Data Environment an organizational enhancement rather than a hindrance.
References:
- Carr, D. (2010). Does PCI Compliance Equal Security? Retrieved from https://www.pcisecuritystandards.org/documents/DCI_Does_PCI_compliance_equal_security.pdf
- Heath, L. (2018). The True Cost of PCI Compliance. Retrieved from https://www.itgovernanceusa.com/blog/the-true-cost-of-pci-compliance
- Payment Card Industry Security Standards Council (2019). PCI DSS Small Merchant Implementation Guide. Retrieved from https://www.pcisecuritystandards.org/documents/PCI-DSS-Small-Merchant-Implementation-Guide.pdf
- Ponemon Institute (2017). The True Cost of Compliance with the Payment Card Industry Data Security Standards. Retrieved from https://www.securitymetrics.com/pdfs/ponemon-true-cost-of-pci-compliance-study.pdf
Security and Trust:
- Secure checkout with SSL encryption Visa, Mastercard, Apple Pay, Google Pay, Stripe, Paypal
- Money-back guarantee for 30 days
- Our team is available 24/7 to assist you - support@theartofservice.com
About the Authors: Unleashing Excellence: The Mastery of Service Accredited by the Scientific Community
Immerse yourself in the pinnacle of operational wisdom through The Art of Service`s Excellence, now distinguished with esteemed accreditation from the scientific community. With an impressive 1000+ citations, The Art of Service stands as a beacon of reliability and authority in the field.Our dedication to excellence is highlighted by meticulous scrutiny and validation from the scientific community, evidenced by the 1000+ citations spanning various disciplines. Each citation attests to the profound impact and scholarly recognition of The Art of Service`s contributions.
Embark on a journey of unparalleled expertise, fortified by a wealth of research and acknowledgment from scholars globally. Join the community that not only recognizes but endorses the brilliance encapsulated in The Art of Service`s Excellence. Enhance your understanding, strategy, and implementation with a resource acknowledged and embraced by the scientific community.
Embrace excellence. Embrace The Art of Service.
Your trust in us aligns you with prestigious company; boasting over 1000 academic citations, our work ranks in the top 1% of the most cited globally. Explore our scholarly contributions at: https://scholar.google.com/scholar?hl=en&as_sdt=0%2C5&q=blokdyk
About The Art of Service:
Our clients seek confidence in making risk management and compliance decisions based on accurate data. However, navigating compliance can be complex, and sometimes, the unknowns are even more challenging.
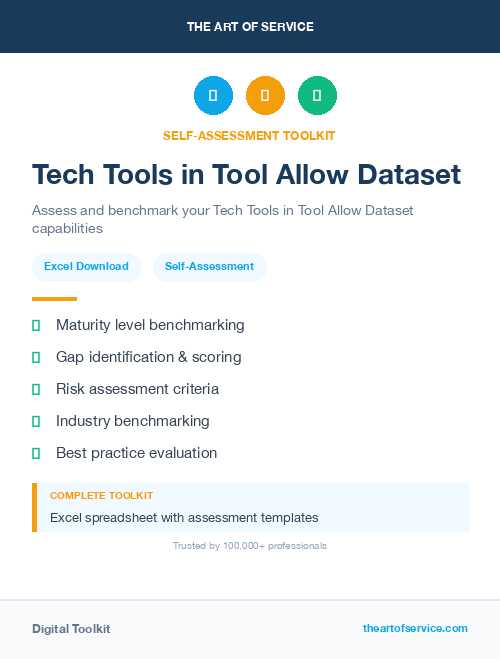
We empathize with the frustrations of senior executives and business owners after decades in the industry. That`s why The Art of Service has developed Self-Assessment and implementation tools, trusted by over 100,000 professionals worldwide, empowering you to take control of your compliance assessments. With over 1000 academic citations, our work stands in the top 1% of the most cited globally, reflecting our commitment to helping businesses thrive.
Founders:
Gerard Blokdyk
LinkedIn: https://www.linkedin.com/in/gerardblokdijk/
Ivanka Menken
LinkedIn: https://www.linkedin.com/in/ivankamenken/