Discover Insights, Make Informed Decisions, and Stay Ahead of the Curve:
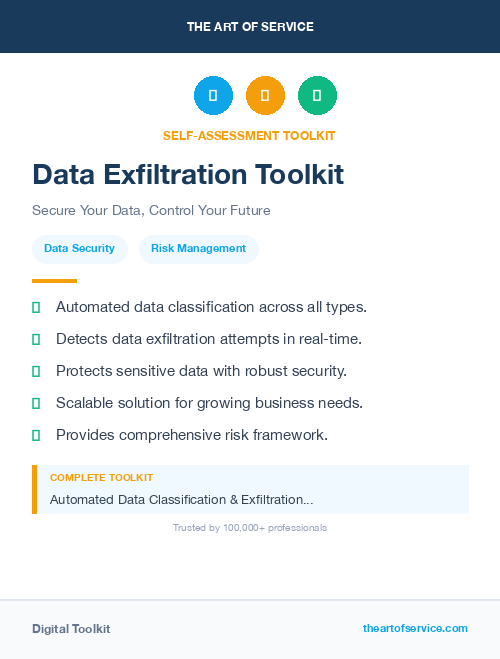
Key Features:
Comprehensive set of 1542 prioritized Data Exfiltration requirements. - Extensive coverage of 127 Data Exfiltration topic scopes.
- In-depth analysis of 127 Data Exfiltration step-by-step solutions, benefits, BHAGs.
- Detailed examination of 127 Data Exfiltration case studies and use cases.
- Digital download upon purchase.
- Enjoy lifetime document updates included with your purchase.
- Benefit from a fully editable and customizable Excel format.
- Trusted and utilized by over 10,000 organizations.
- Covering: ISO 22361, Background Checks, Employee Fraud, Physical Access, Data Loss Prevention, Systems Review, Corporate Fraud, IT Governance, Penetration Testing, Crisis Communication, Safety Training, Social Engineering, Security Investigations, Distribution Strategy, Security Culture, Surveillance Monitoring, Fire Safety, Security Protocols, Network Monitoring, Risk Assessment, Authentication Process, Security Policies, Asset Protection, Security Challenges, Insider Threat Detection, Packet Filtering, Urban Planning, Crisis Management, Financial Crimes, Policy Guidelines, Physical Security, Insider Risks, Regulatory Compliance, Security Architecture, Cloud Center of Excellence, Risk Communication, Employee Screening, Security Governance, Cyber Espionage, Data Exchange, Workplace Safety, DNS policy, Connected Systems, Supply Chain Risk, Cybersecurity Awareness, Threat Mitigation, Chain of Evidence, Implementation Challenges, Future Technology, Physical Threats, Security Breaches, Vulnerability Assessments, IT Security, Workplace Harassment, Risk Management, Facility Access, Fraud Prevention, Supply Chain Security, Cybersecurity Budget, Bug Bounty Programs, Privacy Compliance, Mobile Device Security, Identity Theft, Cyber Threats, Contractor Screening, Intrusion Detection, Executive Protection, Vendor Management, Insider Threats, Cybersecurity Framework, Data Exfiltration, Access Control, Code Consistency, Recognize Team, Workplace Violence, Cloud Compliance, Building Security, IT Staffing, Intellectual Property, Privacy Protection, Remote access controls, Cyber Defense, Hacking Prevention, Private Investigations, Security Procedures, Security Testing, Network Security, Data Protection, Access Management, Security Strategies, Perimeter Security, Cyber Incident Response, Information Technology, Industrial Espionage, Personnel Security, Intelligence Gathering, Cybersecurity Metrics, Social Media Security, Incident Handling, Privacy Training, Security Clearance, Business Continuity, Corporate Vision, DER Aggregation, Contingency Planning, Security Awareness, Business Teams, Data Security, Information Security, Cyber Liability, Security Audits, Facility Security, Data Breach Response, Identity Management, Threat Detection, Disaster Recovery, Security Compliance, IT Audits, Vetting, Forensic Investigations, IT Risk Management, Security Maturity, Threat Modeling, Emergency Response, Threat Intelligence, Protective Services, Cloud Security
Data Exfiltration Assessment Dataset - Utilization, Solutions, Advantages, BHAG (Big Hairy Audacious Goal):
Data Exfiltration
Data Exfiltration involves implementing policies and procedures to prevent unauthorized access by employees to sensitive information and physical facilities within an organization.
- Yes, implementing access control systems can limit unauthorized entry and minimize the risk of insider threats.
- Regularly conducting employee background checks can help identify potential risks and protect against insider threats.
- Implementing employee training programs on security protocols can create awareness and empower employees to report suspicious activity.
- Monitoring and auditing employee activities, such as internet usage and file access, can help identify unusual behavior and potential risks.
- Utilizing data loss prevention software can prevent confidential information from being accessed or shared without proper authorization.
CONTROL QUESTION: Does the organization have policies protecting the physical security of facilities?
Big Hairy Audacious Goal (BHAG) for 10 years from now:
Yes, the organization has robust policies in place for protecting the physical security of facilities. However, in order to ensure maximum protection against insider threats, our goal is to implement automated and advanced Data Exfiltration (IRM) strategies and tools within the next 10 years.
This goal encompasses both proactive and reactive approaches to managing insider risk, including:
1. Real-time monitoring and analysis of employee behavior across all digital platforms, including email, cloud storage, and collaborative tools.
2. Integration of behavioral analytics and machine learning algorithms to detect anomalies and potential insider risks, such as data exfiltration or unauthorized access to sensitive information.
3. Stronger collaboration and information sharing between HR, security, and IT teams to identify and address potential red flags in employee behavior.
4. Implementation of a comprehensive training program to educate employees on the importance of data security and the consequences of risky behavior.
5. Development of a robust incident response plan, including procedures for investigating and mitigating insider threats.
6. Regular assessments and audits to identify any vulnerabilities or gaps in IRM measures, and take corrective actions as needed.
With these efforts, we aim to have a proactive and holistic approach to managing insider risk, ultimately ensuring the safety and security of our facilities, data, and reputation. This will not only protect our organization, but also strengthen our relationships with clients and stakeholders, and uphold the trust they have placed in us.
Customer Testimonials:
"I`ve been searching for a dataset like this for ages, and I finally found it. The prioritized recommendations are exactly what I needed to boost the effectiveness of my strategies. Highly satisfied!"
"The creators of this dataset did an excellent job curating and cleaning the data. It`s evident they put a lot of effort into ensuring its reliability. Thumbs up!"
"I can`t express how impressed I am with this dataset. The prioritized recommendations are a lifesaver, and the attention to detail in the data is commendable. A fantastic investment for any professional."
Data Exfiltration Case Study/Use Case example - How to use:
Introduction:
Data Exfiltration (IRM) is a consulting firm that specializes in identifying and mitigating potential risks posed by employees, contractors, and other insiders within an organization. The company′s services include conducting thorough risk assessments, developing tailored risk management strategies, and implementing robust security measures to safeguard against both physical and cyber threats. The focus of this case study is to analyze whether the organization has policies in place to protect the physical security of its facilities, and if not, provide recommendations for improvement.
Client Situation:
The client for this case study is a large multinational corporation with offices, manufacturing plants, and warehouses located across different regions. The organization employs thousands of employees, contractors, and vendors who have access to its facilities. The company has expressed concerns about potential insider threats to the physical security of its premises, particularly due to recent incidents of theft and unauthorized access to restricted areas. The client has also recognized the need to comply with industry regulations and best practices to ensure the safety of its assets, employees, and information.
Consulting Methodology:
IRM follows a systematic and holistic approach to assess a client′s insider risk posture. The consulting methodology involves four key phases: assessment, analysis, strategy development, and implementation.
In the first phase, a team of IRM consultants conducts a thorough assessment of the client′s existing policies, procedures, and controls related to the physical security of facilities. This involves evaluating measures such as access control, video surveillance, security personnel, and emergency response plans. The goal is to identify any gaps or weaknesses that could potentially increase the risk of physical security breaches.
In the second phase, the findings from the assessment are analyzed to determine the level of risk exposure and potential impact on the organization. This includes considering factors such as the value of assets, likelihood of occurrence, and consequences of a security breach. Based on this analysis, a risk profile is developed to prioritize the identified risks and establish a baseline for further action.
In the third phase, a tailored risk management strategy is developed, with a focus on mitigating high-priority risks. This strategy includes a mix of technical, administrative, and physical controls to enhance the organization′s overall security posture. The recommendations are aligned with best practices, industry standards, and regulatory requirements.
The final phase involves implementing the recommended controls, which may involve working with the client′s IT and security teams to integrate new systems, update policies and procedures, and provide training to employees and contractors.
Deliverables:
1. Risk assessment report: A detailed report outlining the results of the assessment, including identified gaps and weaknesses in the physical security policies and controls.
2. Risk analysis report: A comprehensive report that outlines the level of risk exposure and potential impact of physical security breaches on the organization.
3. Risk management strategy: A tailored risk management strategy that includes specific recommendations to mitigate high-priority risks.
4. Implementation plan: A detailed plan for implementing the recommended controls, including timelines, responsibilities, and cost estimates.
5. Training materials: Training materials and resources to educate employees and contractors on security policies, procedures, and best practices.
Implementation Challenges:
One of the main challenges in implementing policies and measures to protect the physical security of facilities is resistance from employees and contractors who may view them as restrictive and hindering their productivity. Another challenge is ensuring that the recommended controls are integrated seamlessly into the organization′s existing processes and systems. IRM addresses these challenges by involving key stakeholders in the development of the risk management strategy, providing thorough training and awareness programs, and collaborating closely with the client′s IT and security teams during implementation.
Key Performance Indicators (KPIs):
1. Reduction in security incidents: A decrease in the number of physical security incidents such as unauthorized access or theft indicates improved security measures.
2. Compliance with regulations and best practices: Measuring the organization′s compliance with industry regulations and best practices serves as an indicator of its overall risk posture.
3. Employee satisfaction: Conducting employee feedback surveys can assess the effectiveness and impact of the introduced security measures without disrupting daily operations.
4. Timely incident response: Measuring the time taken to respond to a physical security incident helps identify areas for improvement and potential bottlenecks in the response process.
Management Considerations:
Effective management of insider risks requires a proactive and ongoing effort. Thus, it is important for the organization to continuously review and update its physical security policies and procedures to address new threats and vulnerabilities. Additionally, regular training and awareness programs should be conducted to ensure that employees and contractors are aware of their roles and responsibilities in safeguarding the organization′s premises. Regular audits and assessments should also be carried out to monitor the effectiveness of implemented controls and identify any emerging risks.
Conclusion:
In conclusion, the organization does have policies in place to protect the physical security of its facilities; however, there is always room for improvement. IRM′s comprehensive consulting approach helps clients identify and mitigate potential risks to their assets, employees, and information. By conducting thorough assessments, developing tailored strategies, and implementing robust security measures, the organization can significantly reduce its risk exposure and comply with industry regulations and best practices. Ongoing maintenance and continuous improvement will enable the organization to stay ahead of any emerging physical security threats and ensure the safety of its facilities.
Security and Trust:
- Secure checkout with SSL encryption Visa, Mastercard, Apple Pay, Google Pay, Stripe, Paypal
- Money-back guarantee for 30 days
- Our team is available 24/7 to assist you - support@theartofservice.com