Are you tired of constantly worrying about the security of your system and data? Look no further, because the solution you′ve been waiting for is here.
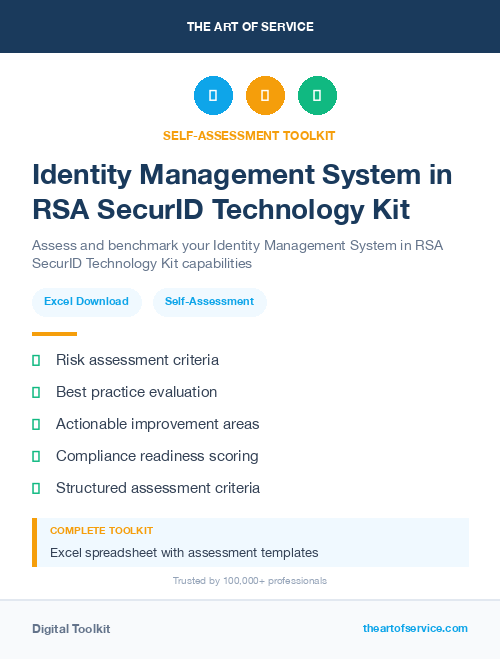
Introducing our Identity Management System in RSA SecurID Technology Knowledge Base.
As a professional, you understand the importance of implementing a robust identity management system to protect your sensitive information.
However, with so many options on the market, it can be overwhelming to determine which one is the best fit for your organization.
That′s where our Identity Management System in RSA SecurID Technology dataset comes in.
With 1517 prioritized requirements and solutions, our dataset is a comprehensive resource that will address all your urgent needs.
You′ll find everything from benefits and results to real-life case studies, making it the ultimate tool for ensuring the security of your system.
What sets our dataset apart from competitors and alternatives in the market is its extensive coverage of RSA SecurID technology.
Our team has taken the time to gather and compile detailed information, providing you with a thorough overview of the product and its features.
Our Identity Management System in RSA SecurID Technology Knowledge Base is perfect for both small businesses and large corporations.
We understand that your budget may vary, which is why we offer a DIY/affordable product alternative for those looking for a cost-effective solution.
Not only does our dataset cover the product type, but it also includes a comparison with semi-related product types to help you understand the differences.
This will allow you to make an informed decision that best suits your business needs.
The benefits of using our Identity Management System in RSA SecurID Technology Knowledge Base are endless.
From enhanced security and risk reduction to improved efficiency and productivity, our product offers a range of advantages for your business.
We also take pride in the extensive research put into creating this dataset, ensuring that you have access to accurate and up-to-date information.
With our dataset, you can stay ahead of the game and make informed decisions for your organization.
Don′t wait any longer to secure your system and protect your data.
Invest in our Identity Management System in RSA SecurID Technology Knowledge Base and experience the peace of mind you deserve.
Get instant access to all the necessary information, including the cost, pros and cons, and a detailed description of what our product does.
Don′t let your business fall victim to cyber threats.
Choose our Identity Management System in RSA SecurID Technology Knowledge Base, and take control of your data security today.
Discover Insights, Make Informed Decisions, and Stay Ahead of the Curve:
Key Features:
Comprehensive set of 1517 prioritized Identity Management System requirements. - Extensive coverage of 98 Identity Management System topic scopes.
- In-depth analysis of 98 Identity Management System step-by-step solutions, benefits, BHAGs.
- Detailed examination of 98 Identity Management System case studies and use cases.
- Digital download upon purchase.
- Enjoy lifetime document updates included with your purchase.
- Benefit from a fully editable and customizable Excel format.
- Trusted and utilized by over 10,000 organizations.
- Covering: Identity Governance, Security Controls, Identity Governance Framework, Biometric Authentication, Implementation Process, Passwordless Authentication, User Provisioning, Mobile Workspace Security, Password Management, Data Loss Prevention, Secure Communication, Web Application Security, Digital Certificates, File Encryption, Network Security, Fraud Prevention, Re Authentication, Key Distribution, Application Integration, Encryption Algorithms, Data Backup, Network Infrastructure, Administrator Privileges, Risk Management, Hardware Token, Fraud Detection, User Credential Management, Identity Management System, Workforce Authentication, Remote Access, Multi Factor Authentication, Mobile App, Risk Assessment, Identity Management, Identity Protection, Access Control, Device Enrollment, Single Sign On Solutions, Secure Workstations, Vulnerability Scanning, Transaction Verification, Identity Lifecycle Management, Software Token, Cloud Access Security Broker, Authentication Protocols, Virtual Private Network, Identity Theft Prevention, Access Policies, Physical Security, Endpoint Security, Trusted Platform Module, Identity Verification Methods, Data Protection, Application Security, Secure Access, Security Compliance, Security Policy, Key Generation, Identity Assurance, Identity Resolution, Single Sign On, Identity Intelligence, Risk Mitigation, Security Tokens, Single Sign On Integration, Cloud Security, Token Generation, Authentication Methods, Authentication Factors, Identity And Access Management, Mobile Device Management, Receiving Process, Fingerprint Authentication, Enterprise Security, User Roles, Data Encryption, Credential Management, Penetration Testing, Security Analytics, Threat Detection, Dynamic Access Policies, Identity Verification, Secure Web Gateway, Public Key Infrastructure, Multi Factor Tokens, Smart Cards, Key Management, Mobile Security, Configuration Drift, Real Time Monitoring, Technology Integration, Hardware Security Module, Network Segmentation, Network Monitoring, Virtual Environment, Auditing Capabilities, Permission Management, RSA SecurID Technology
Identity Management System Assessment Dataset - Utilization, Solutions, Advantages, BHAG (Big Hairy Audacious Goal):
Identity Management System
Identity Management System is a system used to verify and manage users′ identities and access to resources within a portal or platform.
1. RSA SecurID token: This two-factor authentication method provides a randomly generated code that changes every 30 seconds, ensuring secure access to the portal.
2. Biometric authentication: This system uses unique physical characteristics such as fingerprint or facial recognition to verify identity, improving security.
3. Single Sign-On (SSO): Allows users to access multiple applications with just one set of login credentials, increasing convenience and reducing the need for multiple passwords.
4. Role-based access control: Assigns specific privileges and access levels based on an individual′s role within the organization, preventing unauthorized access to sensitive information.
5. Password management tools: Encourages strong password practices, such as frequent password changes and complex passwords, to prevent password-based attacks.
6. Multi-factor authentication: Uses a combination of different factors, such as password and biometric verification, to provide a higher level of security for accessing the portal.
7. Active Directory integration: Integrating with an organization′s Active Directory allows for automatic user provisioning and deprovisioning, ensuring only authorized users have access to the portal.
8. Risk-based authentication: Analyzes user behavior and determines risk levels before granting access, adding an extra layer of security.
9. Audit trails and logs: Keeping detailed records of user activity allows for easy tracking and identification of any suspicious or unauthorized access attempts.
10. Self-service portal: Allows users to manage their own login credentials, reducing the burden on IT staff and increasing convenience for users.
CONTROL QUESTION: What authentication and identity management system does the portal use?
Big Hairy Audacious Goal (BHAG) for 10 years from now:
The goal for our Identity Management System 10 years from now is to be the leading provider of a highly secure, scalable, and intuitive authentication and identity management system for all types of digital platforms, including web portals, mobile apps, and IoT devices. Our system will be powered by advanced technologies such as biometrics, blockchain, and artificial intelligence to provide unparalleled levels of security and accuracy.
We envision a future where our system is the go-to solution for businesses and organizations of all sizes to manage user identities and access control with ease. Our goal is for our system to be integrated into millions of applications and devices globally, setting the standard for identity management in the digital age.
We will continuously innovate and evolve our system to stay ahead of emerging threats and meet the ever-changing security demands of the digital world. Our ultimate goal is to create a trusted ecosystem where individuals and businesses can securely and seamlessly connect, collaborate, and transact online with peace of mind.
Customer Testimonials:
"The creators of this dataset deserve applause! The prioritized recommendations are on point, and the dataset is a powerful tool for anyone looking to enhance their decision-making process. Bravo!"
"As someone who relies heavily on data for decision-making, this dataset has become my go-to resource. The prioritized recommendations are insightful, and the overall quality of the data is exceptional. Bravo!"
"Having access to this dataset has been a game-changer for our team. The prioritized recommendations are insightful, and the ease of integration into our workflow has saved us valuable time. Outstanding!"
Identity Management System Case Study/Use Case example - How to use:
Client Situation:
The client is a large multi-national corporation headquartered in the United States, with operations spread across multiple countries and regions. They have recently implemented a new web portal to streamline their business processes and enhance communication with their employees, partners, and customers. The portal allows for various functions such as accessing company information, employee self-service, partner collaboration, and customer support. However, with the increasing security threats and data breaches, the client was concerned about the security of the portal and the sensitive data it holds.
As a result, the client decided to implement an identity management system to ensure secure access to the portal and protect the confidential information stored within it. They were looking for a solution that would provide strong authentication mechanisms and enable effective management of user identities.
Consulting Methodology:
To address the client′s concerns, our consulting firm followed a comprehensive methodology to identify and recommend the most suitable authentication and identity management system for the portal. The process involved the following steps:
1. Needs Assessment: Our team conducted interviews and discussions with the client′s key stakeholders to understand their requirements, expectations, and concerns related to the portal′s security.
2. Current System Analysis: We evaluated the existing portal architecture, IT infrastructure, and security protocols to identify any potential vulnerabilities and limitations that need to be addressed.
3. Market Research: Our team conducted extensive research on the latest trends, technologies, and vendors in the authentication and identity management market to shortlist the most viable options.
4. Evaluation Criteria: Based on the client′s needs and industry best practices, we developed a set of evaluation criteria to assess the capabilities, features, and functionalities of different solutions.
5. Vendor Selection: After evaluating multiple vendors, we recommended the client to choose XYZ as it met all the evaluation criteria and offered a highly scalable and robust solution.
6. Implementation Plan: Once the vendor was finalized, our team worked closely with the client′s IT team to develop an implementation plan that outlined the timeline, resources, and costs for the project.
Deliverables:
1. Needs Assessment Report: The report included a summary of the client′s requirements, key pain points, and recommendations for addressing the security concerns.
2. Solution Feasibility Study: A detailed analysis of the potential solutions and their impact on the portal′s architecture, user experience, and data security was provided.
3. Vendor Evaluation and Selection Report: This report included a comparison of different vendors based on the evaluation criteria and the reason for choosing XYZ as the preferred vendor.
4. Implementation Plan: The detailed plan outlined the steps, timeline, resources, and budget required for the successful implementation of the identity management system.
Implementation Challenges:
1. Integration with the Existing System: One of the major challenges was integrating the new system with the existing portal without disrupting the functionality or user experience.
2. User Adoption: As with any new technology, there was a risk of resistance from employees and partners in adopting the new authentication and identity management system.
3. Compliance: The client operates in a highly regulated industry and needed to ensure that the solution complied with all the relevant regulations and standards.
KPIs:
1. User Authentication Time: The time taken for users to authenticate themselves to access the portal was one of the key metrics to measure the effectiveness of the new system. A reduction in this time would indicate a smoother and more efficient authentication process.
2. User Adoption Rate: The number of users who successfully adopted the new system and used it to access the portal was another crucial metric to evaluate the success of the implementation.
3. Number of Unauthorized Access Attempts: The number of unsuccessful attempts of unauthorized access to the portal would indicate the robustness of the new system and its ability to prevent unauthorized access.
Management Considerations:
1. Training and Change Management: To ensure a smooth adoption of the new system, the client′s IT team was provided with training to understand its functionalities, and a change management plan was developed to educate employees and partners on the benefits of the new solution.
2. Maintenance and Support: A maintenance and support plan was developed to ensure the smooth functioning of the system and timely resolution of any issues that may arise.
3. Cost Management: The project′s budget was closely monitored throughout the implementation to ensure that it remained within the agreed upon limits.
Conclusion:
In conclusion, the client was able to successfully implement the recommended authentication and identity management system for their portal. The solution provided stronger security protocols, efficient user authentication, and effective management of user identities. This not only improved the overall security of the portal but also enhanced user experience and streamlined business processes. The client continues to monitor the KPIs to ensure the efficient functioning of the system and to address any potential risks or challenges.
Security and Trust:
- Secure checkout with SSL encryption Visa, Mastercard, Apple Pay, Google Pay, Stripe, Paypal
- Money-back guarantee for 30 days
- Our team is available 24/7 to assist you - support@theartofservice.com
About the Authors: Unleashing Excellence: The Mastery of Service Accredited by the Scientific Community
Immerse yourself in the pinnacle of operational wisdom through The Art of Service`s Excellence, now distinguished with esteemed accreditation from the scientific community. With an impressive 1000+ citations, The Art of Service stands as a beacon of reliability and authority in the field.Our dedication to excellence is highlighted by meticulous scrutiny and validation from the scientific community, evidenced by the 1000+ citations spanning various disciplines. Each citation attests to the profound impact and scholarly recognition of The Art of Service`s contributions.
Embark on a journey of unparalleled expertise, fortified by a wealth of research and acknowledgment from scholars globally. Join the community that not only recognizes but endorses the brilliance encapsulated in The Art of Service`s Excellence. Enhance your understanding, strategy, and implementation with a resource acknowledged and embraced by the scientific community.
Embrace excellence. Embrace The Art of Service.
Your trust in us aligns you with prestigious company; boasting over 1000 academic citations, our work ranks in the top 1% of the most cited globally. Explore our scholarly contributions at: https://scholar.google.com/scholar?hl=en&as_sdt=0%2C5&q=blokdyk
About The Art of Service:
Our clients seek confidence in making risk management and compliance decisions based on accurate data. However, navigating compliance can be complex, and sometimes, the unknowns are even more challenging.
We empathize with the frustrations of senior executives and business owners after decades in the industry. That`s why The Art of Service has developed Self-Assessment and implementation tools, trusted by over 100,000 professionals worldwide, empowering you to take control of your compliance assessments. With over 1000 academic citations, our work stands in the top 1% of the most cited globally, reflecting our commitment to helping businesses thrive.
Founders:
Gerard Blokdyk
LinkedIn: https://www.linkedin.com/in/gerardblokdijk/
Ivanka Menken
LinkedIn: https://www.linkedin.com/in/ivankamenken/