Look inside the Kanban:
Make sure the GRC team is responsible for providing oversight and governance over all cybersecurity related activities to ensure management awareness, maintain risk metrics, and mature the security and compliance posture of the environment.
Benefits of the Cybersecurity Maturity Model Certification Kanban
- What level of maturity does your organization have for cybersecurity monitoring and logging activities?
- What exposure does your organizations senior management have into your cybersecurity practices?
- What cybersecurity risks will you have from greater connectivity of operational technology?
- What level of maturity will your organization need to be certified to?
- Do the inherent risk profile and Cybersecurity maturity levels meet managements business and risk management expectations?
- Does your organization have a mechanism in place to ensure that the actions of individual system users can be uniquely traced for accountability purposes?
- What fundamental elements should be in place to accelerate a financial organizations cybersecurity maturity and maintain a high level once it is attained?
- Which capability maturity model do you currently use to assess cybersecurity maturity?
- Do any new features that may increase cybersecurity risk also have an increased benefit?
- Is your organization ready to increase visibility, improve situational awareness, enhance compliance and mature your ICS cybersecurity posture?
Summary
The Art of Service has identified and prioritized 2303 Cybersecurity Maturity Model Certification critical capabilities and use cases to assess and use. Leaders can select those results that best align with their business needs before implementing a solution.
The Art of Service's Critical Capabilities evaluates and prioritizes hundreds of results to help with the outcome selection process.
This Critical Capabilities Kanban will enable leaders to shortlist hundreds of appropriate results fast, because they are uniquely ready-to-use prioritized, starting with the 'Must Have' category; the most urgent and critical priorities.
This Kanban will help you plan and manage your Cybersecurity Maturity Model Certification roadmap.
- Transform the data into actionable views for your organization: business data changes, so how you view it should be flexible. Create the perfect view that's right for you.
- Put your workflows on autopilot: Help your team go faster and focus on what matters by automating your processes. Upload and use the Kanban with your favorite apps and services like Asana, Airtable, Basecamp, Monday.com, Atlassian, Trello etc.
- Knock down data silos: Align your teams around a single source of truth with real-time data from different sources. Point. Click. Stay in Sync.
- Use it's flexible reporting for your unique use case: Whether you're "no-code" or you "know-code", the Kanban is the foundational tool to show what you want to who needs to see it.
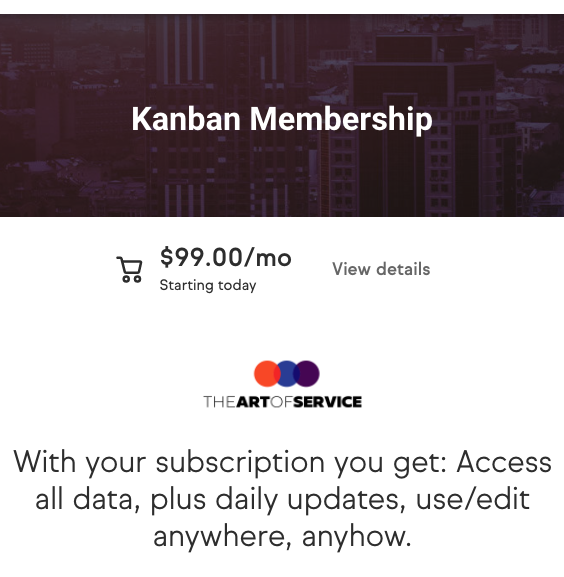
Included in your instant download purchase are the following digital products:
As seen in the Kanban above, the complete 2303 Cybersecurity Maturity Model Certification critical capabilities and use cases, their prioritization, workflows, tagging and questions.
The download is available as an easy to re-use Excel format, which you can use as is, or import in any management tool of your choice, like Monday.com, Atlassian, Smartsheet, Power BI, Asana, Airtable etc.
Also included is the Cybersecurity Maturity Model Certification critical capabilities Book in PDF format covering all the criteria including ideas for (potential) roles to assign the criteria to. Table of contents:
About The Art of Service
Cybersecurity Maturity Model Certification Critical Capabilities, Meaningful Metrics And Their Prioritization
Background
Prioritization Of Requirements
The Prioritization Categories Are:
- Must Have
- Should Have
- Ought to Have
- Might Have
- Could Have
Use In New Product/Service/Process Development
Benefits
The Critical Cybersecurity Maturity Model Certification Capabilities And Their Priorities:
- Priority - Must Have #
- Priority - Should Have #
- Priority - Ought to Have #
- Priority - Might Have #
- Priority - Could Have #
Index
You're in good company. Join:
Trusted by: Audax Labs, West Advanced Technologies (WATI), Ensono, Labcorp, Highbrow-Tech, General Dynamics Information Technology, Datavail, Atos, The Exchange, Vadam Group, Reasons could include: the employer is not accepting applications, is not actively hiring, or is reviewing applications, TIBCO Software, BMC Software, FIS Global, JPMorgan Chase Bank, N.A., Qlik, Deloitte, OPULENTSOFT, CapB InfoteK, SAIC, Capgemini, USAA, Denken Solutions Inc, Senior Architects, Luxoft, Cognizant Technology Solutions, Mantek Solutions, United Airlines Inc., DMI, Diaconia LLC, Costco Wholesale, Ivy Tech Solutions inc, Morgan Stanley, Brown Brothers Harriman, CitiusTech, Raley's Supermarkets, Pinnacle Group, BNY Mellon, Micro Focus, TTI, INC., DXC, Frontier Communications, Amazon Web Services, Inc., eClerx LLC, Farm Credit Bank of Texas, HSBC, Criterion Systems, Inc., Amplify Systems, Essendant Co., Dine Development Corporation, Berry Global, Inc, Accenture, VertexOne, Peraton, American Unit, Creative Information Technology, Inc, Pyramid Systems, Inc., Safran, Boston Consulting Group, Astronautics/Kearfott Corporation, Keiter, New York University, Sila SG, Microsoft, BD, The Geneva Foundation, Contracting Resources Group, KPMG, Parsons, Corporate Headquarters, University of Maine, Collins Aerospace, BAE Systems, Wipfli LLP