Warrant that your organization provides Information security knowledge and skills in managing the administration of Information security Services under general guidance.
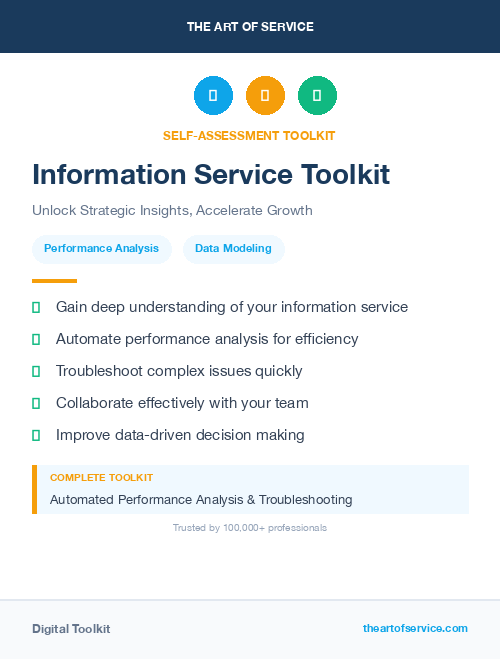
More Uses of the Information security Services Toolkit:
- Establish: team up with colleagues in other lines of services in support of Client Needs for Information security Services.
- Methodize: effectively contribute to the development of controls and processes improving Information security Services.
- Initiate: Information security Services.
- Evaluate: Information security Services Strategy.
- Provide guidance to your organization on the appropriate Information security Services, mechanisms and technologies.
- Ensure your design contributes to the creation of department procedures, standards and documentation for all Information security Services.
- Ensure your planning complies; teams up with colleagues in other lines of services in support of Client Needs for Information security Services.
- Devise: intern, Information security Services.
- Supervise: Information security Services policy.
Save time, empower your teams and effectively upgrade your processes with access to this practical Information security Services Toolkit and guide. Address common challenges with best-practice templates, step-by-step Work Plans and maturity diagnostics for any Information security Services related project.
Download the Toolkit and in Three Steps you will be guided from idea to implementation results.
The Toolkit contains the following practical and powerful enablers with new and updated Information security Services specific requirements:
STEP 1: Get your bearings
Start with...
- The latest quick edition of the Information security Services Self Assessment book in PDF containing 49 requirements to perform a quickscan, get an overview and share with stakeholders.
Organized in a Data Driven improvement cycle RDMAICS (Recognize, Define, Measure, Analyze, Improve, Control and Sustain), check the…
- Example pre-filled Self-Assessment Excel Dashboard to get familiar with results generation
Then find your goals...
STEP 2: Set concrete goals, tasks, dates and numbers you can track
Featuring 999 new and updated case-based questions, organized into seven core areas of Process Design, this Self-Assessment will help you identify areas in which Information security Services improvements can be made.
Examples; 10 of the 999 standard requirements:
- What are your key Information security Services indicators that you will measure, analyze and track?
- How do you do Risk Analysis of rare, cascading, catastrophic events?
- How long to keep data and how to manage retention costs?
- Who are your Key Stakeholders who need to sign off?
- Is the need for Organizational Change recognized?
- When you map the key players in your own work and the types/domains of relationships with them, which relationships do you find easy and which challenging, and why?
- Who pays the cost?
- How do you cross-sell and up-sell your Information security Services success?
- What is effective Information security Services?
- What goals did you miss?
Complete the self assessment, on your own or with a team in a workshop setting. Use the workbook together with the self assessment requirements spreadsheet:
- The workbook is the latest in-depth complete edition of the Information security Services book in PDF containing 994 requirements, which criteria correspond to the criteria in...
Your Information security Services self-assessment dashboard which gives you your dynamically prioritized projects-ready tool and shows your organization exactly what to do next:
- The Self-Assessment Excel Dashboard; with the Information security Services Self-Assessment and Scorecard you will develop a clear picture of which Information security Services areas need attention, which requirements you should focus on and who will be responsible for them:
- Shows your organization instant insight in areas for improvement: Auto generates reports, radar chart for maturity assessment, insights per process and participant and bespoke, ready to use, RACI Matrix
- Gives you a professional Dashboard to guide and perform a thorough Information security Services Self-Assessment
- Is secure: Ensures offline Data Protection of your Self-Assessment results
- Dynamically prioritized projects-ready RACI Matrix shows your organization exactly what to do next:
STEP 3: Implement, Track, follow up and revise strategy
The outcomes of STEP 2, the self assessment, are the inputs for STEP 3; Start and manage Information security Services projects with the 62 implementation resources:
- 62 step-by-step Information security Services Project Management Form Templates covering over 1500 Information security Services project requirements and success criteria:
Examples; 10 of the check box criteria:
- Cost Management Plan: Eac -estimate at completion, what is the total job expected to cost?
- Activity Cost Estimates: In which phase of the Acquisition Process cycle does source qualifications reside?
- Project Scope Statement: Will all Information security Services project issues be unconditionally tracked through the Issue Resolution process?
- Closing Process Group: Did the Information security Services Project Team have enough people to execute the Information security Services Project Plan?
- Source Selection Criteria: What are the guidelines regarding award without considerations?
- Scope Management Plan: Are Corrective Actions taken when actual results are substantially different from detailed Information security Services Project Plan (variances)?
- Initiating Process Group: During which stage of Risk planning are risks prioritized based on probability and impact?
- Cost Management Plan: Is your organization certified as a supplier, wholesaler, regular dealer, or manufacturer of corresponding products/supplies?
- Procurement Audit: Was a formal review of tenders received undertaken?
- Activity Cost Estimates: What procedures are put in place regarding bidding and cost comparisons, if any?
Step-by-step and complete Information security Services Project Management Forms and Templates including check box criteria and templates.
1.0 Initiating Process Group:
- 1.1 Information security Services project Charter
- 1.2 Stakeholder Register
- 1.3 Stakeholder Analysis Matrix
2.0 Planning Process Group:
- 2.1 Information security Services Project Management Plan
- 2.2 Scope Management Plan
- 2.3 Requirements Management Plan
- 2.4 Requirements Documentation
- 2.5 Requirements Traceability Matrix
- 2.6 Information security Services Project Scope Statement
- 2.7 Assumption and Constraint Log
- 2.8 Work Breakdown Structure
- 2.9 WBS Dictionary
- 2.10 Schedule Management Plan
- 2.11 Activity List
- 2.12 Activity Attributes
- 2.13 Milestone List
- 2.14 Network Diagram
- 2.15 Activity Resource Requirements
- 2.16 Resource Breakdown Structure
- 2.17 Activity Duration Estimates
- 2.18 Duration Estimating Worksheet
- 2.19 Information security Services project Schedule
- 2.20 Cost Management Plan
- 2.21 Activity Cost Estimates
- 2.22 Cost Estimating Worksheet
- 2.23 Cost Baseline
- 2.24 Quality Management Plan
- 2.25 Quality Metrics
- 2.26 Process Improvement Plan
- 2.27 Responsibility Assignment Matrix
- 2.28 Roles and Responsibilities
- 2.29 Human Resource Management Plan
- 2.30 Communications Management Plan
- 2.31 Risk Management Plan
- 2.32 Risk Register
- 2.33 Probability and Impact Assessment
- 2.34 Probability and Impact Matrix
- 2.35 Risk Data Sheet
- 2.36 Procurement Management Plan
- 2.37 Source Selection Criteria
- 2.38 Stakeholder Management Plan
- 2.39 Change Management Plan
3.0 Executing Process Group:
- 3.1 Team Member Status Report
- 3.2 Change Request
- 3.3 Change Log
- 3.4 Decision Log
- 3.5 Quality Audit
- 3.6 Team Directory
- 3.7 Team Operating Agreement
- 3.8 Team Performance Assessment
- 3.9 Team Member Performance Assessment
- 3.10 Issue Log
4.0 Monitoring and Controlling Process Group:
- 4.1 Information security Services project Performance Report
- 4.2 Variance Analysis
- 4.3 Earned Value Status
- 4.4 Risk Audit
- 4.5 Contractor Status Report
- 4.6 Formal Acceptance
5.0 Closing Process Group:
- 5.1 Procurement Audit
- 5.2 Contract Close-Out
- 5.3 Information security Services project or Phase Close-Out
- 5.4 Lessons Learned
Results
With this Three Step process you will have all the tools you need for any Information security Services project with this in-depth Information security Services Toolkit.
In using the Toolkit you will be better able to:
- Diagnose Information security Services projects, initiatives, organizations, businesses and processes using accepted diagnostic standards and practices
- Implement evidence-based Best Practice strategies aligned with overall goals
- Integrate recent advances in Information security Services and put Process Design strategies into practice according to Best Practice guidelines
Defining, designing, creating, and implementing a process to solve a business challenge or meet a business objective is the most valuable role; In EVERY company, organization and department.
Unless you are talking a one-time, single-use project within a business, there should be a process. Whether that process is managed and implemented by humans, AI, or a combination of the two, it needs to be designed by someone with a complex enough perspective to ask the right questions. Someone capable of asking the right questions and step back and say, 'What are we really trying to accomplish here? And is there a different way to look at it?'
This Toolkit empowers people to do just that - whether their title is entrepreneur, manager, consultant, (Vice-)President, CxO etc... - they are the people who rule the future. They are the person who asks the right questions to make Information security Services investments work better.
This Information security Services All-Inclusive Toolkit enables You to be that person.
Includes lifetime updates
Every self assessment comes with Lifetime Updates and Lifetime Free Updated Books. Lifetime Updates is an industry-first feature which allows you to receive verified self assessment updates, ensuring you always have the most accurate information at your fingertips.