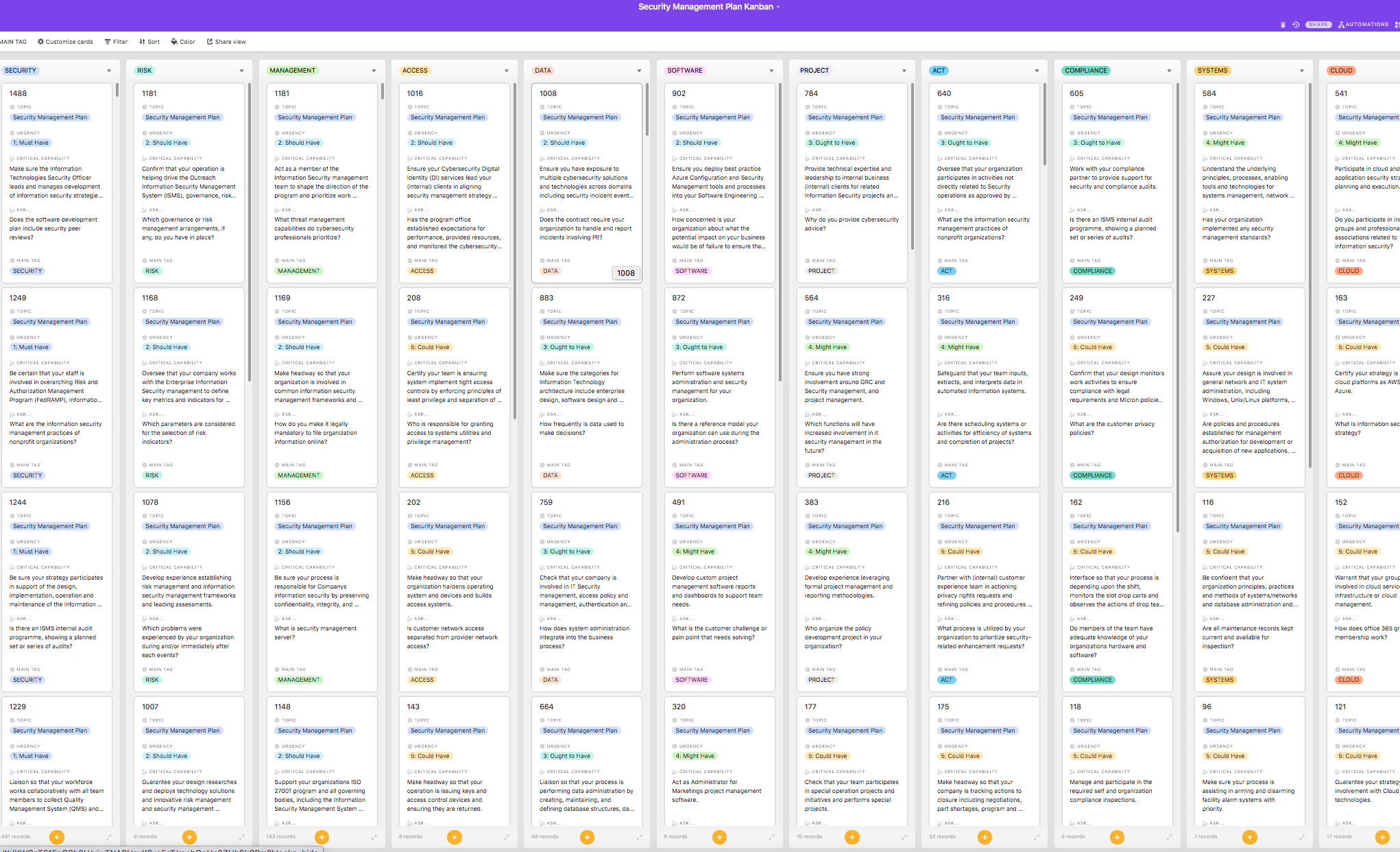
Look inside the Kanban:
https://theartofservice.com/Security-Management-Plan-kanban
Make sure the Information Technologies Security Officer leads and manages development of information security strategies and plans to prevent the unauthorized use, release, modification, loss or destruction of data and other information assets; facilitates the involvement of key stakeholders in plan development processes designed to assess the business impacts of various security approaches and develop security plans that balance security needs with business operational requirements, stakeholders and team members; leads and participates in plan development tasks, including conducting risk assessments; evaluating security management options; developing procedures and protocols, including designating and training of primary and backup recovery teams, develops and implements comprehensive communications plans and tools.
Benefits of the Security Management Plan Kanban
- Increase information security management automation in the context of a process model.
- Effectively secure data when the security solutions that exist have already been broken.
- Restrict, log, and monitor access to your information security management systems.
- Manage software configuration in your development and testing environment (e.g., automated tools, spreadsheets, data storage, etc.).
- Ensure CSP has implemented security controls to mitigate third party risks.
- Prove data provenance in a cloud computing scenario when you are using shared resources.
- Know supply chain risk has been addressed.
- Assess your organizations security posture and gain comfort around security management as a whole.
- Ensure your staff and organization follow the points made on the left to ensure you get the best performance from the Security Team.
- Establish and ensure a Data Owner controlled users access to data.
Summary
The Art of Service has identified and prioritized 1185 Security Management Plan critical capabilities and use cases to assess and use. Leaders can select those results that best align with their business needs before implementing a solution.
The Art of Service's Critical Capabilities evaluates and prioritizes hundreds of results to help with the outcome selection process.
This Critical Capabilities Kanban will enable leaders to shortlist hundreds of appropriate results fast, because they are uniquely ready-to-use prioritized, starting with the 'Must Have' category; the most urgent and critical priorities.
This Kanban will help you plan and manage your Security Management Plan roadmap.
- Transform the data into actionable views for your organization: business data changes, so how you view it should be flexible. Create the perfect view that's right for you.
- Put your workflows on autopilot: Help your team go faster and focus on what matters by automating your processes. Upload and use the Kanban with your favorite apps and services like Asana, Airtable, Basecamp, Monday.com, Atlassian, Trello etc.
- Knock down data silos: Align your teams around a single source of truth with real-time data from different sources. Point. Click. Stay in Sync.
- Use it's flexible reporting for your unique use case: Whether you're "no-code" or you "know-code", the Kanban is the foundational tool to show what you want to who needs to see it.
Included in your instant download purchase are the following digital products:
As seen in the Kanban above, the complete 1185 Security Management Plan critical capabilities and use cases, their prioritization, workflows, tagging and questions.
The download is available as an easy to re-use Excel format, which you can use as is, or import in any management tool of your choice, like Monday.com, Atlassian, Smartsheet, Power BI, Asana, Airtable etc.
Also included is the Security Management Plan critical capabilities Book in PDF format covering all the criteria including ideas for (potential) roles to assign the criteria to. Table of contents:
About The Art of Service
Security Management Plan Critical Capabilities, Meaningful Metrics And Their Prioritization
Background
Prioritization Of Requirements
The Prioritization Categories Are:
- Must Have
- Should Have
- Ought to Have
- Might Have
- Could Have
Use In New Product/Service/Process Development
Benefits
The Critical Security Management Plan Capabilities And Their Priorities:
- Priority - Must Have #
- Priority - Should Have #
- Priority - Ought to Have #
- Priority - Might Have #
- Priority - Could Have #
Index
You're in good company. Join:
Trusted by: Capgemini, iknowvate technologies, KION Group AG, Cisco Meraki, Virginia Tech, Environmental Defense Fund, Abbott Laboratories, USAA, Datadog, Wells Fargo, Optiv, Azzur Group, Huntington Bank, PacifiCorp, John Deere, Biogen, AIG, The Ohio State University, Cloudflare, Ferguson, Netskope, PG&E Corporation, Federal Reserve Bank of New York, University of North Carolina at Chapel Hill, Agama Solutions, Wyze Labs, Barnes, Dennig & Co., Ltd., Eastman, Booz Allen Hamilton, DocuSign, S&P Global, Portland General Electric, Rockwell Automation, Hewlett Packard Enterprise, OhioHealth, Premier Staffing Partners, Harvard Pilgrim Health Care, Abbvie, KPMG, The Walt Disney Company (Corporate), LogMeIn, Liberty, CareJourney, Industrial Scientific Corporation, Weld County, CO, Principal Financial Group, TransUnion, Callaway Golf Company, Kemper, BD, Relias LLC, Blue Shield of California, LG&E and KU Energy, Chevron Phillips Chemical Company, Topgolf, PulteGroup, Honeywell, Federal Reserve Bank of San Francisco, Deutsche Bank, Humana, Premera Blue Cross, EMMES, RELATION INSURANCE INC, Nuvance Health, Verizon, University of Arizona Global Campus, Area 1 Security, Dataminr, Starbucks, Fairview Health Services, iHeartMedia, Inc., Palo Alto Networks, AT&T, Lutron Electronics, Infinity Consulting Solutions, Inc., International Data Group, Inc., Datto Jobs, Costco Wholesale, Blue Yonder, Norfolk Southern Corp, Amazon Data Services, Inc., Stifel Financial Corp., CitiusTech, Vouch Insurance, NTT DATA Business Solutions, Robinhood, ARM Treasure Data, Bravent, II-VI, Cincinnati Children's Hospital, Wayfair, StackPath, Match Group, Logitech, Lindsay, AlignTech, Cognosante, LLC, The Hanover Insurance Group, Paradigm, Carpe Data, Integrated Data Services Inc., Amazon.com Services LLC, LSEG (London Stock Exchange Group), Johnson & Johnson Family of Companies, Security PS, VMware, Walmart, MetLife, ProQuest LLC, Databricks, Gap Inc., Molina Healthcare, XIFIN, CrowdStrike, WSSC Water, Amazon Dev Center U.S., Inc., Datto Inc., The Climate Corporation, Zscaler, Fiserv, Flexport, National Security Agency, Great American Insurance Group, Princeton University, On Q Financial, Synchrony, Morgan Stanley, IBM, Lumen, Capital One, CyberArk, Charles Schwab, Farmers Insurance Group, Deloitte, Dell Technologies, Allstate, Fannie Mae, TitanHouse, Inc., Square, University of Colorado, Avaya, US House of Representatives, Apple, Indeed, Anthem, Nike, NJ Transit, Aurora, George Washington University, EY Global Services Limited prod, Google, Amazon Web Services, Inc., Cisco Systems, Saviynt, IDENTIFY SECURITY, University of California Santa Cruz, Accenture, Signify, GE Healthcare, Interos, Inc., Mutual of Omaha, PDI, Salesforce, Atomic, FireEye, Inc., PRICE WATERHOUSE COOPERS, Central Intelligence Agency